Ransomware in 2026: How Groups Are Actually Getting In (And Why You’re Missing It)
Ransomware attacks are evolving fast in 2026. Learn how attackers gain access, why businesses miss the signs, and how to stop attacks earlier.

Introduction: The Threat Is Evolving Faster Than Your Defences
Ransomware isn’t slowing down, it’s accelerating and adapting.
Attackers are continuously refining how they gain access, bypass controls, and monetise breaches across organisations of all sizes. Global ransomware damages are expected to reach $57 billion in 2025, highlighting just how lucrative and scalable these operations have become.
At the same time, threat actors are shifting strategy. Nearly every industry experienced an increase in cyber attacks in 2024, with attackers deliberately targeting sectors that are less mature in their security posture.
This is the reality of ransomware in 2026: it’s no longer just about encryption. It’s about access, speed, automation, and leverage.
The Real Scale of Ransomware (And Why You’re Underestimating It)
The numbers we see only tell part of the story.
- Ransomware attacks increased by 34% in 2025
- In the U.S. alone, incidents rose by 50% in the first 10 months
- 5,010 attacks were reported in 2025 vs 3,335 in 2024
But here’s the critical gap:
Up to 85% of ransomware attacks go unreported.
This means most organisations are benchmarking their risk against incomplete data, while attackers operate with far greater visibility through underground forums, leak sites, and shared intelligence.
Why Small Businesses Are the Primary Target
Ransomware groups are not just chasing big names anymore. In fact, they’re increasingly focused on organisations that are easier to compromise.
- 88% of ransomware incidents involve small and midsize businesses
- Over two-thirds of attacks (2024–2025) targeted companies with fewer than 500 employees
Why?
Because smaller organisations often:
- Lack dedicated threat intelligence capabilities
- Have limited visibility across their digital footprint
- Struggle with patching, monitoring, and incident response
For attackers, this creates the perfect balance of low resistance and high likelihood of payment.
How Ransomware Groups Are Actually Getting In
The biggest misconception about ransomware is that it’s deployed instantly. In reality, most attacks follow a structured intrusion lifecycle. And in 2026, that lifecycle is faster, stealthier, and increasingly automated.
1. Initial Access Brokers (IABs)
Attackers are buying access instead of hacking it themselves. Compromised credentials, exposed RDP services, and vulnerable VPNs are sold on the dark web, allowing ransomware affiliates to skip the hardest part of the attack.
2. Phishing and Social Engineering 2.0
Traditional phishing still works, but it’s now enhanced by AI.
Attackers are using:
- AI-generated emails tailored to employees
- Deepfake voice messages impersonating executives
- Highly contextual lures based on leaked data
This dramatically increases success rates and reduces detection.
3. Exploiting the Expanding Attack Surface
Modern organisations are more exposed than ever. From cloud environments to APIs, attackers are identifying weak entry points across:
- Misconfigured cloud storage
- Unsecured APIs
- Third-party integrations
4. Living Off the Land
Once inside, attackers avoid detection by using legitimate tools. Instead of deploying obvious malware, they:
- Use built-in admin tools (PowerShell, WMI)
- Move laterally across networks
- Escalate privileges quietly
By the time ransomware is deployed, the attacker already has full control.
What’s Changing in 2026: The Next Wave of Ransomware
Ransomware is evolving beyond manual operations into highly automated ecosystems.
AI-Driven Worm Epidemics
Self-propagating ransomware will spread across networks without human input, identifying vulnerabilities and moving laterally in real time. This reduces attack time from days to minutes.
Why Attackers Target Downtime-Critical Industries
Ransomware isn’t random. It’s strategic.
Attackers prioritise sectors where disruption is not an option:
- Healthcare
- Manufacturing
- Logistics
- Financial services
The logic is simple, the higher the cost of downtime, the higher the likelihood of payment. This is why ransomware has evolved into a business model, not just a tactic.
The Defence Needs to Evolve Too
Traditional security approaches are no longer enough. In 2026, organisations need to shift from reactive to proactive defence by focusing on:
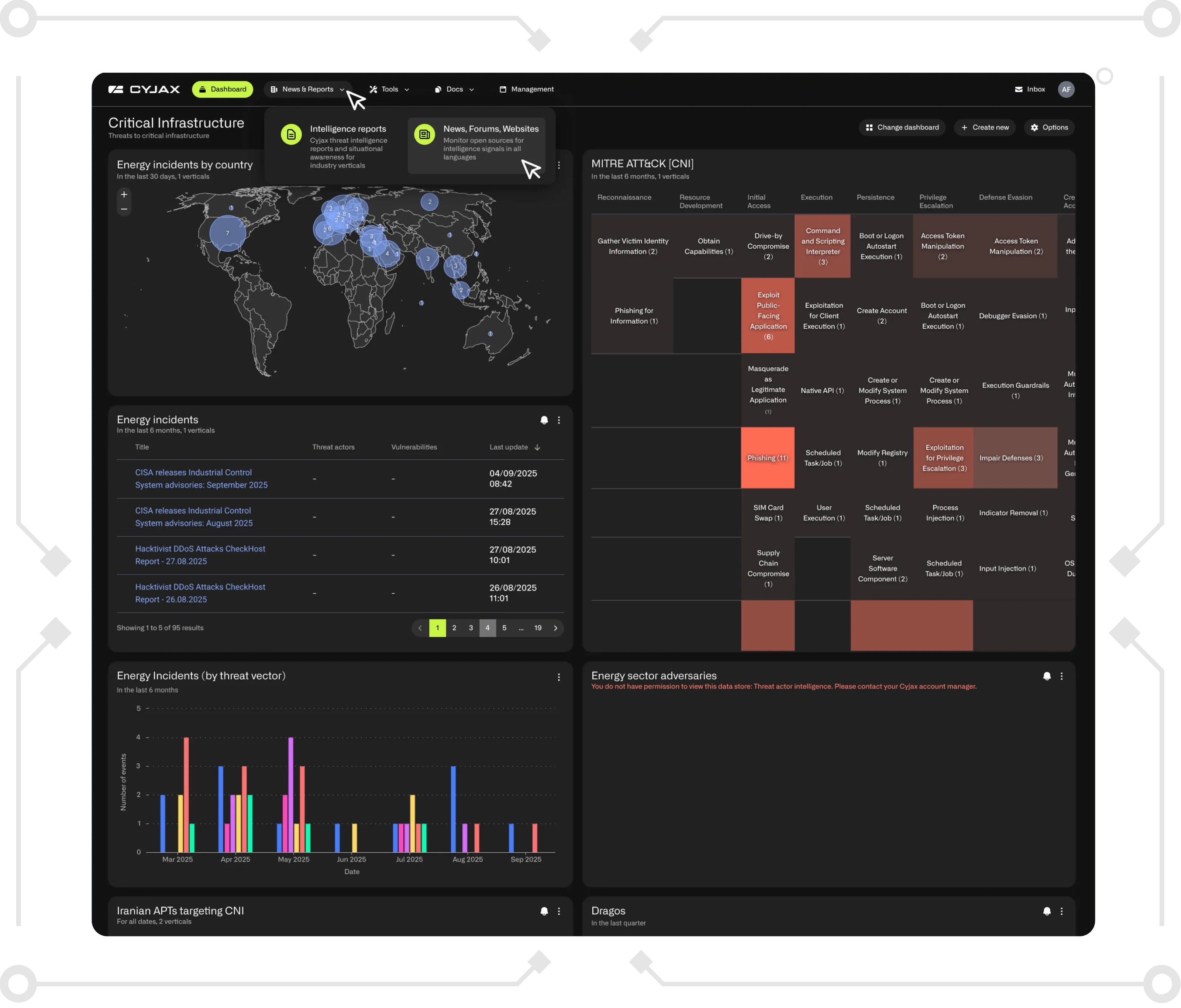
- External threat visibility across the dark web and open sources
- Attack surface monitoring to identify exposures before attackers do
- Threat intelligence integration into decision-making
Ransomware groups are already operating with speed, automation, and intelligence. To keep up, defenders need the same.
See what attackers see before they act.
Book a demo with CYJAX to uncover exposed assets, monitor emerging ransomware threats, and stay ahead of intrusion activity before it escalates.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.