The Top 10 Requirements MSSPs Have for External CTI
For MSSPs, CTI isn’t useful unless it's relevant, fast, actionable, reliable - and backed by human analysts and flexible delivery. When those boxes are checked, CTI becomes a strategic force, not just background noise.

Introduction
MSSPs operate high-availability Security Operations Centres (SOCs), which enable them to deliver 24/7 security services designed to reduce the burden on enterprises in staffing and maintaining operational security capabilities.
MSSPs play a pivotal role by extending security operations on behalf of their clients. They provide continuous visibility and protection across diverse environments, enabling organisations to maintain a mature security posture without the need to recruit, train, and retain large internal security teams.
However, MSSPs operate under constant pressure to deliver demonstrable value. They must provide rapid threat detection and mitigation, reduce risk across varied industries, and sustain resilient security operations. Achieving this consistently, and at scale, relies on one critical component: Cyber Threat Intelligence (CTI).
When delivered effectively, Cyber Threat Intelligence transforms raw data into actionable insight. It enriches MSSP operations with relevance, timeliness, and clarity, enabling a transition from reactive defence to proactive threat management. High quality CTI empowers MSSPs to anticipate emerging threats, reduce noise, and drive decisive responses, thereby strengthening the trust and effectiveness of their services.
Not all Cyber Threat Intelligence, however, meets these standards. For MSSPs, the distinction between valuable intelligence and wasted effort depends on the quality, relevance, and usability of the intelligence provided. Raw feeds without contextual filtering introduce noise and consume analyst resources, whereas structured, timely, and actionable intelligence enhances detection and response across multiple client environments. At CYJAX, we work with leading MSSPs, including Cyro Cyber and Fortress, to ensure they receive intelligence that delivers measurable value.
The following outlines the ten primary requirements MSSPs place on external CTI, representing the factors that determine whether intelligence functions as a strategic enabler or an operational burden.
Key Requirements for External CTI in MSSP Operations
- Relevance and Client Context Mapping
For CTI to be genuinely useful, it must be filtered and enriched so that it directly aligns with each MSSP client’s industry, geography, technology stack and current threat posture. Raw intelligence feeds without contextual filtering add little value, consume analyst time unnecessarily and introduce operational noise that detracts from meaningful detection and response.
- Timeliness of Intelligence
Speed is a decisive factor in the value of CTI. MSSPs require high-confidence indicators of compromise and vulnerability intelligence before threats are widely weaponised. Delayed intelligence quickly loses its value; in many cases, timeliness outweighs completeness, as early warning enables proactive defence.
- Actionability and Integration Readiness
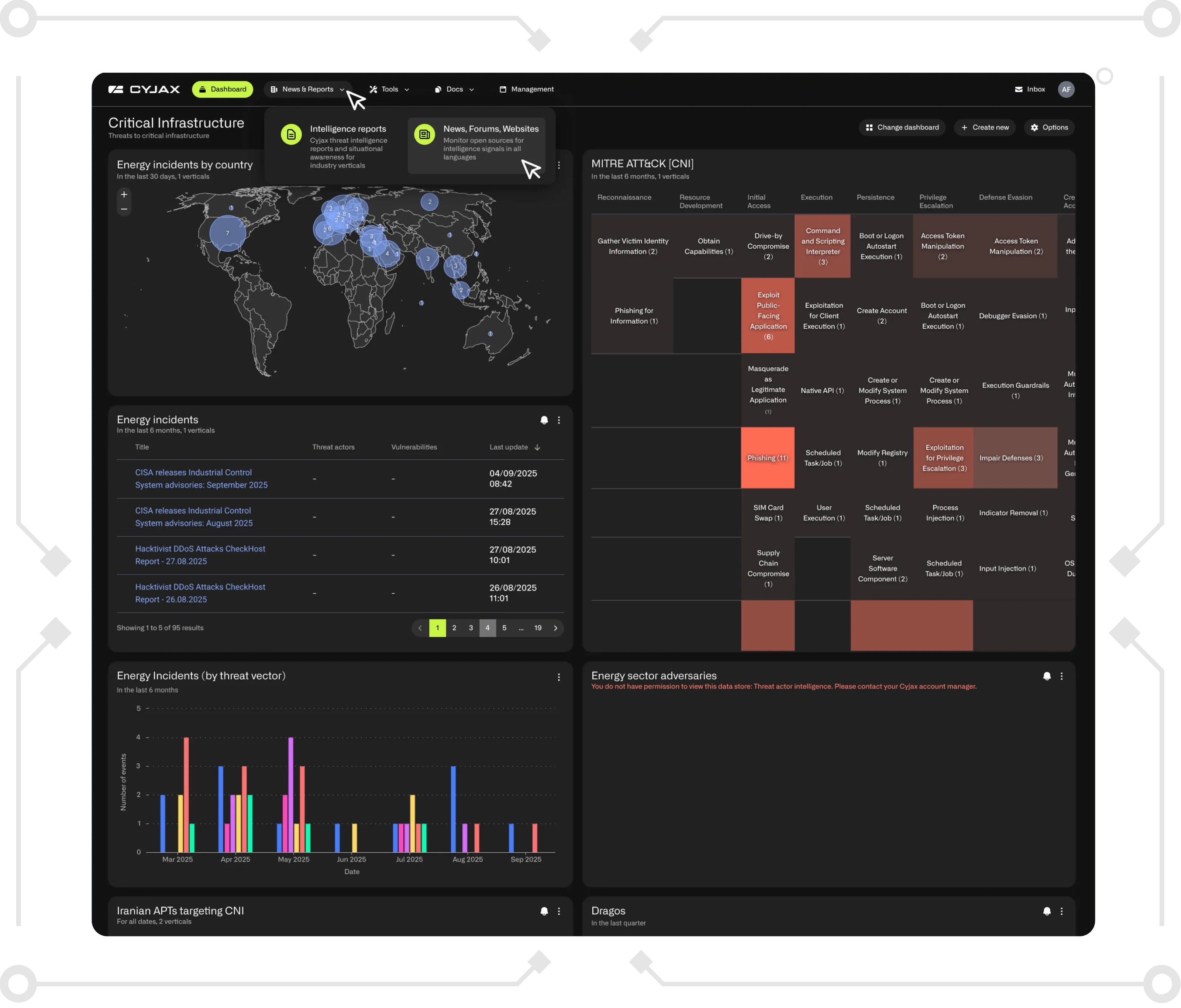
CTI must be delivered in a form that MSSPs can act upon immediately. This includes compatibility with common formats such as JSON, STIX and TAXII, as well as the ability to push intelligence directly into SIEM and SOAR platforms. Prebuilt detection and hunting rules, along with mapping to frameworks such as MITRE ATT&CK and the cyber kill chain, ensure analysts can respond effectively without diverting resources to formatting and translation tasks.
- High Fidelity and Low Noise
Excessive false positives reduce efficiency and strain analyst resources. High-quality CTI must incorporate strong false-positive control, confidence scoring and deduplication. Equally important is prioritisation based on evidence of exploitation in the wild, rather than on theoretical vulnerabilities or industry hype.
- Enrichment and Attribution
Indicators alone rarely provide sufficient insight for MSSPs. Effective CTI must include context around threat actors, their tactics, techniques and procedures, as well as their motivations and historical campaigns. This enrichment enables analysts to pivot rapidly from a single indicator to a broader campaign analysis, without relying on multiple vendors or tools.
- Sector and Geo-Specific Intelligence
A generic approach to CTI is insufficient for MSSPs, which serve diverse verticals and geographical regions. Intelligence must be tailored to the specific industries under protection, such as finance, healthcare or manufacturing, and reflect the regional threat landscape, particularly where clients operate in high-risk geographies.
- Analyst Support and Human-on-the-Loop
Technology cannot address every intelligence requirement. MSSPs benefit significantly from access to skilled CTI analysts who can conduct deep-dive investigations, provide rapid turnaround on ad hoc queries from SOC teams and deliver surge support during major incidents. This human element ensures that intelligence remains both operationally relevant and strategically valuable.
- Consistency and Reliability of Delivery
The effectiveness of CTI depends on its reliability. MSSPs require assurance that intelligence feeds will not suffer outages or contain outdated data. Regular and predictable delivery of tactical, operational and strategic intelligence outputs is essential to maintain trust and ensure operational continuity.
- Transparent Source and Methodology
MSSPs are often required to justify the intelligence they provide to clients. Transparency regarding data sources and the methodologies used for risk and confidence scoring is therefore critical. Clear and auditable practices not only build trust with MSSPs but also support their clients’ own compliance and assurance processes.
- Flexible Licensing and Multi-Tenant Support
Licensing arrangements can either facilitate or hinder the effective use of CTI. MSSPs require flexible models that support multi-tenant environments, enable scalability through API keys and per-tenant filtering, and allow the delivery of CTI to multiple downstream customers without creating legal or operational obstacles.
Conclusion
MSSPs face the ongoing challenge of delivering measurable security outcomes while managing diverse client environments and evolving threats. As outlined above, the value of external Cyber Threat Intelligence lies in its ability to be relevant, timely, actionable, and reliable meeting the ten critical requirements that determine whether CTI strengthens operations or adds unnecessary noise.
Through its dedicated MSSP Programme, CYJAX addresses these needs directly. By providing enriched, sector-specific and integration-ready intelligence, supported by experienced analysts and transparent methodologies, CYJAX enables MSSPs to enhance detection, streamline response, and deliver greater value to their clients. In doing so, CYJAX helps MSSPs move beyond reactive defence and establish CTI as a genuine strategic advantage.
For MSSPs seeking to strengthen their threat intelligence capabilities, contact CYJAX to explore how their MSSP Programme can deliver timely, actionable, and client-focused intelligence.
Receive our latest cyber intelligence insights delivered directly to your inbox
Simply complete the form to subscribe to our newsletter, ensuring you stay informed about the latest cyber intelligence insights and news.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.

.png)