Threat Actors to Watch: May 2026 | Top Cyber Threat Groups Targeting Organisations
Discover the top threat actors to watch in May 2026, including OilRig, Cozy Bear, Lazarus, and Charming Kitten. Learn how leading cyber threat groups operate, who they target, and how organisations can stay protected.
-5.png)
Introduction
Cyber security teams that focus only on incidents often miss the bigger picture. Looking at threat actors rather than isolated attacks changes how organisations assess risk, prioritise defences, and prepare for future threats. Understanding who is behind an attack, how they typically operate, and what they target gives security leaders the ability to anticipate campaigns before damage occurs, rather than simply reacting after the fact.
In 2026, the threat landscape is becoming more selective and more strategic. Attackers are increasingly focused on precision, persistence, and high-value impact rather than mass disruption. Ransomware activity may decline in overall volume, but incidents are likely to become more severe and financially damaging. Meanwhile, Ransomware-as-a-Service (RaaS) ecosystems continue to evolve into modular criminal operations, making attacks more efficient and scalable.
At the same time, advanced groups are adopting AI-assisted reconnaissance, automated phishing, and stealthier in-memory intrusion techniques. Critical sectors such as manufacturing, healthcare, energy, logistics, and public services remain key targets due to their operational importance and lower tolerance for downtime.
Below are four threat actors security teams should monitor closely in May 2026.
OilRig
OilRig is a long-running Iranian state-linked cyber espionage group active since at least 2014. It has historically targeted organisations considered strategically important to Iran, including government bodies, telecommunications providers, and regional enterprises across the Middle East, Asia, and the United States.
The group is known for regularly adapting its tooling, malware, and intrusion methods to avoid detection. OilRig often focuses on credential theft, persistence, and intelligence gathering over destructive activity.
Why Watch in May 2026
As geopolitical tensions continue to influence cyber operations, OilRig remains relevant due to its focus on surveillance, regional disruption, and attacks against strategic infrastructure.
Cozy Bear
Cozy Bear, also known as APT29, Nobelium, or Midnight Blizzard, is one of Russia’s most sophisticated cyber espionage groups. Active since at least 2008, it has targeted governments, defence organisations, research institutions, think tanks, and political bodies, particularly across Europe and NATO-aligned countries.
The group became globally known for major campaigns including the Democratic National Committee breach and the SolarWinds supply chain compromise. Cozy Bear is associated with Russia’s foreign intelligence service, the SVR.
Why Watch in May 2026
Cozy Bear remains a high-priority threat due to its advanced stealth tactics, patience, and focus on long-term intelligence collection. Organisations with sensitive data or government links should remain vigilant.
Lazarus Group
Lazarus is one of the world’s most active and financially motivated state-sponsored threat groups. Linked to North Korea, it has targeted banks, cryptocurrency platforms, healthcare organisations, manufacturers, governments, and media companies worldwide.
The group uses a wide range of tactics including phishing, supply chain compromise, zero-day exploitation, malware deployment, espionage, and cryptocurrency theft. Lazarus has been tied to some of the largest digital asset heists ever recorded.
Why Watch in May 2026
As sanctions pressure continues, Lazarus is expected to remain highly active in cryptocurrency theft, financial fraud, and espionage campaigns designed to generate revenue and gather intelligence.
Charming Kitten
Charming Kitten, also known as APT35 or Magic Hound, is another Iran-linked threat actor known for phishing-led intrusion campaigns and intelligence gathering. The group has targeted governments, energy providers, military entities, critical infrastructure, journalists, and policy organisations across the Middle East, Europe, and the Americas.
It commonly relies on credential theft, password spraying, vulnerability exploitation, and web compromise to gain access. Once inside, it focuses on data collection, persistence, and operational disruption.
Why Watch in May 2026
Charming Kitten remains dangerous due to its aggressive social engineering tactics and continued interest in politically sensitive organisations and critical sectors.
Strengthen Cyber Security Against Threat Actors
Threat actors are becoming more adaptive, more specialised, and harder to detect through traditional security monitoring alone. Understanding attacker behaviour, preferred sectors, infrastructure, and evolving tactics is now essential for proactive defence.
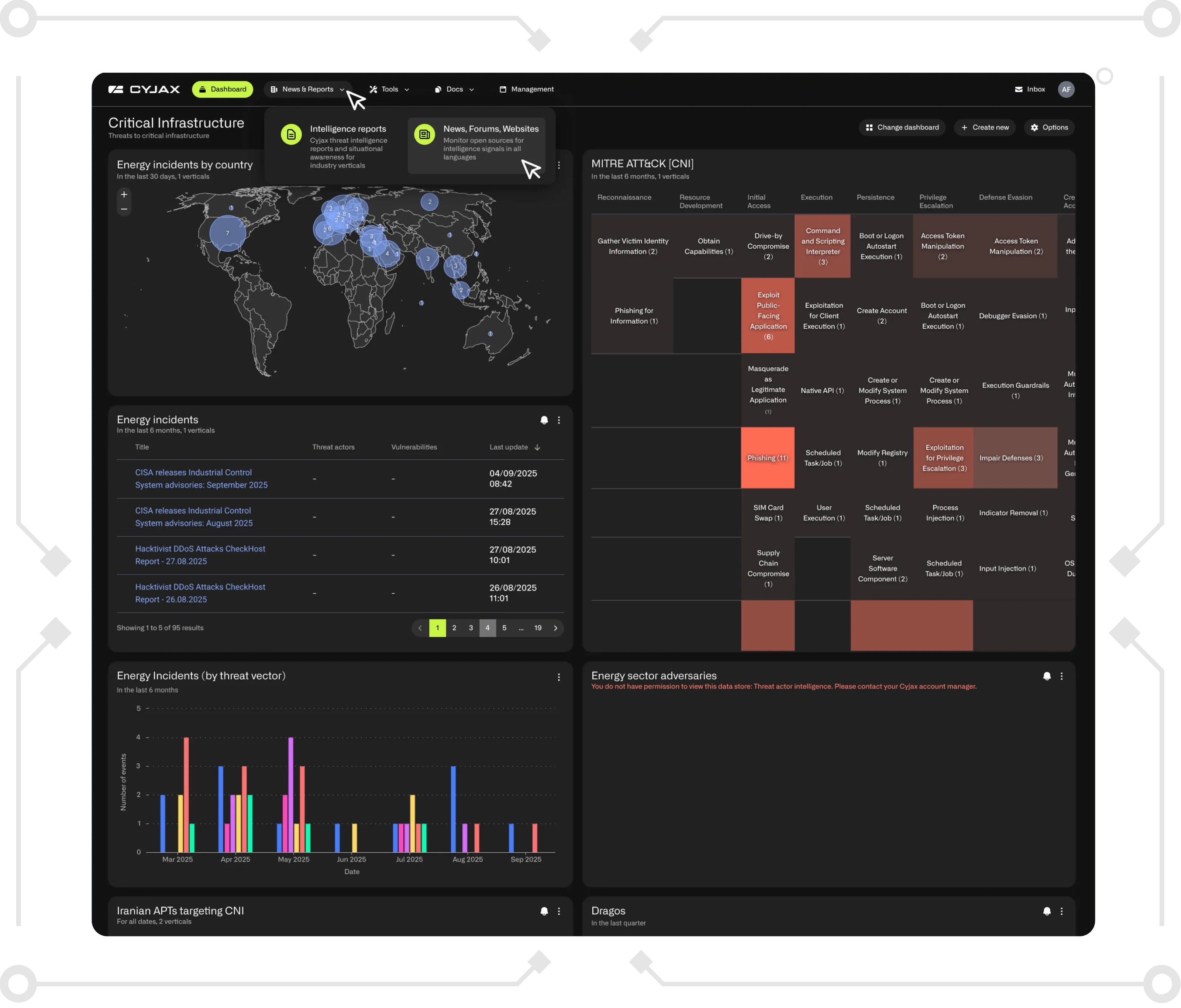
With the right cyber threat intelligence, organisations can identify emerging risks earlier, prioritise genuine threats, and respond with greater confidence. At CYJAX, we help organisations track threat actors, monitor external exposure, and turn intelligence into action.
Book a Demo
See how CYJAX can help your team stay ahead of evolving cyber threats with actionable intelligence, automated monitoring, and real-world context. Book a demo today.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.

-4.png)

