How to Save Time by Using Validated IOCs, So Your Analysts Don’t Have To
Learn how validated IOCs reduce false positives, improve SOC efficiency and give analysts time back by delivering contextual, high-confidence threat intelligence.

SOC analysts begin each shift facing a relentless stream of alerts driven by indicators of compromise (IOCs). Many of these alerts are false positives, some are outdated, and only a small fraction genuinely reflect malicious activity. However, by the time your team manually validates each one, attackers have moved laterally and exfiltrated data.
This is the reality SOC teams live with every day. According to the 2025 SANS Detection & Response Survey, 73% of organisations list false positives as their number one challenge, a dramatic rise from last year.
The problem here isn't a lack of staff or even a lack of intelligence; it's a lack of validated, actionable intelligence. And it's costing organisations significant time, money, and long-term security implications.
The cost of raw IOC feeds
The impact on SOC teams continues to escalate, with over half feeling overwhelmed by alert volume. Analysts report spending over 25% of their time handling false positives, citing this as a top pain point.
ISC2's 2025 Cybersecurity Workforce Study found that 47% of cybersecurity professionals feel overwhelmed by the workload, whilst 48% feel exhausted from trying to stay current on the latest threats and emerging technologies. When you spend hours each day manually validating IOCs, that exhaustion is inevitable.
Automated IOC extraction from threat reports pulls in non-malicious artifacts constantly. Legitimate domains like github.com get flagged when they're mentioned in threat actor TTPs. File hashes for benign Microsoft-signed executables appear because a report discussed how attackers abuse trusted binaries. IP addresses that were malicious six months ago but are now legitimate CDN infrastructure? Still triggering alerts. Security researcher infrastructure? Misclassified as malicious.
Without human validation, these artifacts poison your detection rules. Teams burn hours chasing infrastructure that was never a threat. The burnout is real, triggering expensive recruitment cycles that further strain your operations.
More feeds don't automatically equate to better security. More validated intelligence does.
What “validated” means in practice
"Validated" isn't just a marketing buzzword, it's a standard that separates intelligence from noise. For an IOC to be truly useful in day-to-day detection and response, it must satisfy three criteria: context, confidence, and currency.
1. Context
A raw indicator (an IP address, domain or hash) tells you almost nothing on its own. Context turns a string of characters into actionable insight. Validated intelligence enriches that indicator with information such as associated threat actors, campaigns or tactics, and observed activity that is relevant to your sector..
For example, an address linked to a known command-and-control server used in an active campaign targeting UK financial services is immediately prioritised, not lost amid pages of low-value alerts.
2. Confidence
When multiple independent sources report the same indicator, confidence increases dramatically. But human validation catches what automation misses. An automated system flags 8.8.8.8 (Google DNS) as malicious because a threat report mentioned attackers using it, missing the crucial context. High-reputation threat intelligence sources carry more weight than statistical or ML-based engines with higher false positive rates. Confidence scoring enables tiered workflows where high-confidence IOCs trigger automatic blocking, medium generates alerts, and low populates watchlists.
3. Currency.
Threat actors actively rotate infrastructure. An IOC that was meaningful six months ago may have long since been retired or reassigned to legitimate use. Intelligence that does not age out stale indicators creates noise rather than insight. Effective validation includes lifecycle assessments, ensuring that alerts reflect current and credible threats.
Without context, confidence and currency, intelligence becomes a historical record rather than a tool for operational decision-making.
Reducing hours of triage to minutes
In a typical SOC workflow, an alert generated by a raw IOC often means analysts must manually investigate:
- External threat intelligence platforms
- Open-source threat research
- Internal logs and asset context
- Indicators of related campaigns or actors
Even experienced analysts can spend hours on such verification, time they could spend on proactive tasks such as threat hunting or strategic defence.
Validated IOCs change the equation. When alerts arrive enriched with context and confidence assessments, analysts can rapidly determine severity and next steps. This supports safer automation. High-confidence indicators can inform blocklists and detection rules without introducing excessive false-positive risk.
For lean teams in particular, validated intelligence functions as a force multiplier. It frees analysts to focus on threat hunting, adversary tracking and proactive risk reduction rather than repetitive verification tasks.
Why Human Validation Still Matters
AI can process vast volumes of data. It cannot understand business nuance.
Machine learning models trained on noisy data replicate that noise. They struggle to distinguish between a VPN exit node and attacker-owned infrastructure, or between a legitimate SaaS platform abused by adversaries and infrastructure directly controlled by them.
Industry research shows that hybrid approaches (automation for scale and humans for validation) improve precision and efficiency far beyond what either could achieve alone. In the 2025 IBM breach report, organisations that combined automation with structured security practices saw greater reductions in breach lifecycles than those that relied solely on manual processe.
Give your analysts their time back
Most organisations already have IOC feeds. The question is whether those feeds cost more than they're worth.
If your analysts are drowning in false positives, chasing stale indicators, or spending the majority of their day manually enriching alerts with context, you're not running a modern SOC. You're subsidising your vendor's lack of quality control.
Validated IOCs improve analyst efficiency, team morale, and organisational resilience. They let lean teams focus on threat hunting, strategic defence, and proactive risk reduction.
In 2026, with attack speeds accelerating and analyst burnout at crisis levels, validation isn't a luxury. It's the difference between a team that's constantly reactive and one that's operationally ahead.
Give your analysts their time back. Let them hunt threats, not clean data.
Get Started
Request a free intelligence assessment to find out how much time your SOC is losing to unvalidated IOCs.
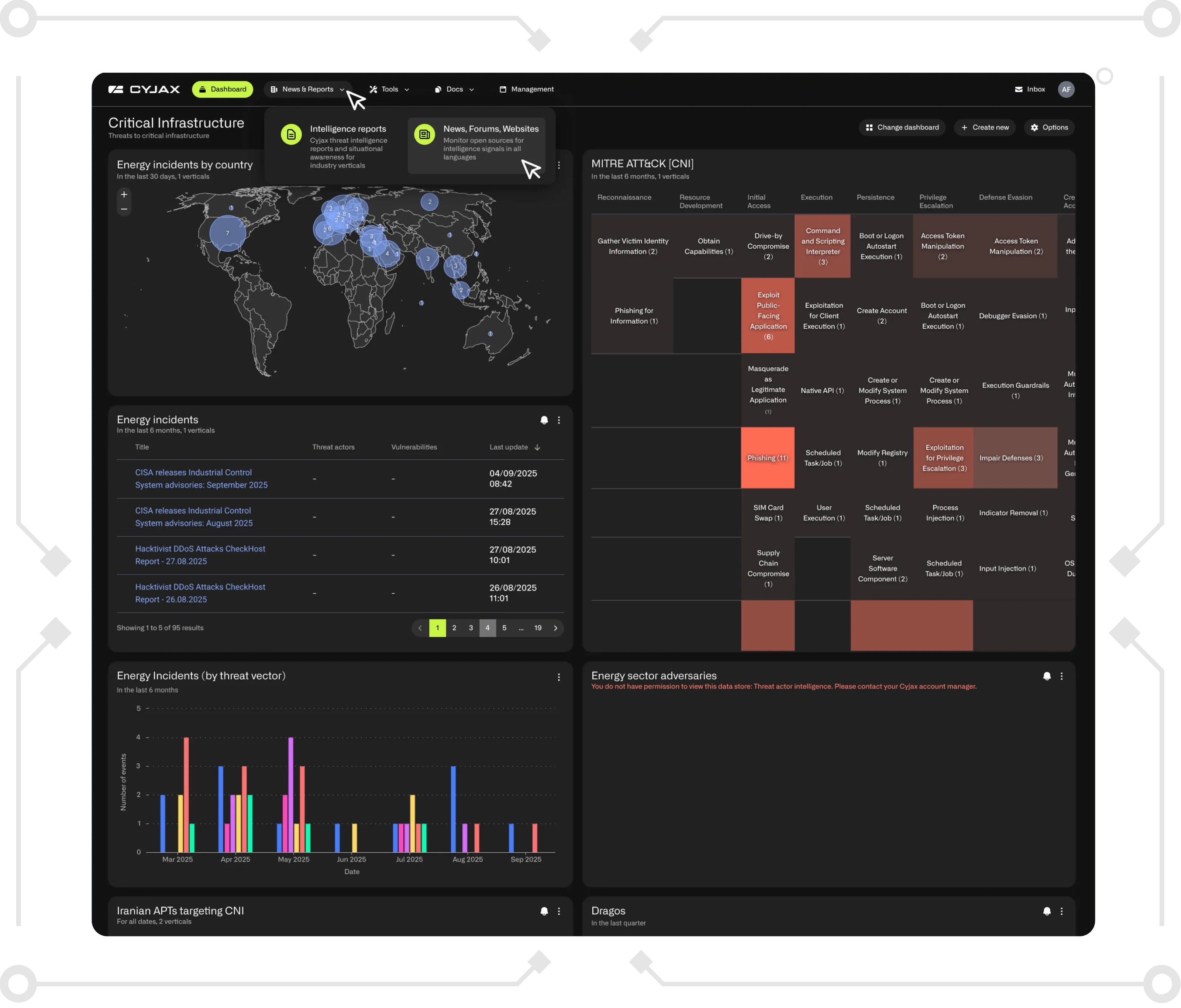
See analyst-enriched intelligence in action by booking a CYJAX demo.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.

-5.png)
-4.png)
