An exploration of information exposure on document sharing platforms
Employees (and even individuals) are unwittingly leaking sensitive data when uploading documents to public sharing platforms. Internal docs, email threads, credentials, and medical reports - all made public because default settings or Google indexing expose them. What appears to be innocent or routine sharing can turn into a threat, including cyberespionage, reputational damage, and insider risk. Awareness and strict document-handling policies aren’t nice to have - they’re essential.

Introduction
Public document libraries and hosting services are websites which host content such as academic and legal papers, work templates, and more. Occasionally, these services allow users to freely search, read, and upload documents without requiring a subscription. This can lead to incidents where content is uploaded without a user’s full understanding of the ramifications of making such documents public. In a professional setting, this can lead to internal or confidential documents being uploaded directly by employees without pre-approval by their organisation.
Cyjax conducts open-source intelligence (OSINT) investigations to identify potential public threats to organisations, including the exposure of protected assets. In mid-August 2025, a significant and diverse range of likely personal and internal documents were identified on a document sharing site. The exposed data ranged from internal documents and corporate email threads to personal information such as licences, bills, full credentials, and more.
It is important to note that these uploads do not exclusively appear to be intentional data breaches by malicious entities. It is likely that employees are uploading documents to services like this to share with other individuals within organisations. Additionally, individuals appear to be uploading personal documents to easily share with third parties. However, on many of these services, uploaded documents are publicly visible and can be searched and viewed by visitors, either through inbuilt search features or Google indexing. As such, information such as personal data, confidential communication, and internal business documents may be publicly exposed through these services.
Cyjax’s findings
Exposed documents
These exposed documents included, but were not limited to, confidential information such as:
- Non-disclosure agreements.
- Employment offers.
- Training documents.
- Personal medical reports and injury claims.
- Defined corporate processes, policies, and procedures.
- Government employee salary and benefit offers.
- Law enforcement-related files.
- Examination answer files from universities.
All of these documents and various others contained confidential and handling classifications, such as those shown in Figure 1. The documents related to enterprises in a wide range of sectors, revenues, and geographies. Much of the exposure identified in this investigation included documents ranging from individuals’ data and internal documents belonging to large enterprises.
Figure 1 – A collection of observed document handling condition notices.
Whilst the documents contained these classifications, highlighting that they were intended to remain private to the organisation, one document sharing site creates AI-enhanced descriptions of the files. This site used the technology to analyse the content and provide context to any uploaded documents. Whilst not containing full confidential information, one observed document simply included a “proprietary & confidential” classification. The AI-enhanced description was “The document is marked as proprietary and confidential, indicating that it contains sensitive information that is not to be disclosed to unauthorized parties”. This site contains a function which searches the title, description, and written content within uploads, allowing users to directly identify potentially sensitive information within documents.
As explained above, this exposure was not limited only to organisations’ documents. Many individuals appear to use these services to upload potentially sensitive documents such as bills, invoices, and email communication with enterprises. This exposes their full names, addresses, account numbers, and occasionally limited financial information. Users were also observed uploading back-up codes and plaintext passwords, likely using the services as private cloud file hosting sites rather than for its intended purpose.
Cyjax tested the timeline from upload to exposure on one document hosting site where public exposure was observed. After creating an account on the service, it took 30 minutes from upload for the file to appear in search results if it was set to publicly available. This setting is enabled by default, which may be why exposure on these sites is common. The document also appeared on Google searches, indicating that the link was added to the sitemap and was visible by crawlers. However, when deleting the file, it was immediately removed from searches, allowing rectification of unintentional exposure.
Indexed documents
A common issue with file hosting and document sharing sites is that even if designed to be secure and private, pages can be indexed by search engines and become publicly accessible. An example of this is AnonFiles. When this secure file hosting site was active, some entries were indexed by Google, allowing users to utilise Google dorking to identify uploaded documents. This site was taken down in 2023 following significant abuse of the platform. However, this technique remains applicable to similar operating services.
For example, one observed site allows users to upload an unlimited volume of files in PDF, Microsoft Word, and PowerPoint formats. This service is mainly used to host tutorials, guides, research, news, and fiction. It does not appear to have a search function. However, Cyjax observed Google indexing files uploaded to the site. This allows users to identify files using this technique. Another observed document sharing platform allowed visitors to use the search functions to identify files of interest without requiring accounts. Both examples highlight how potentially malicious actors might identify files which may have been uploaded without the intention of them being publicly accessible.
Abuse of document sharing platforms
From analysis, Cyjax believes that this type of public exposure can be abused in multiple ways:
- Cyberespionage – If confidential or internal files are publicly exposed, information regarding an organisation’s goals, plans, and intellectual property (IP) can be collected and used as intelligence.
- Data leaks – Threat actors can leak documents in a more public manner to cause reputational damage to organisations. This can significantly affect organisations, particularly when an employee uploaded the document.
- Potential attack leads – Cyjax has observed documents explaining the layout of internal infrastructure and tutorials on how to use proprietary tools offered by organisations. Technical information may be used to identify vulnerable instances or expose internal infrastructure which could be abused as an initial access vector.
- Insider threat - In multiple cases of documents identified by Cyjax, the uploader’s username corresponded to current employees of the organisation which appeared to own the document. Alternatively, the uploader appeared to be the recipient of intended internal communication. This was particularly prevalent in sensitive documents, such as CVs likely sent to an organisation and uploaded by a HR employee or procurement team. This was confirmed through LinkedIn and represents a potential threat vector. An attacker could identify internal documents and the user which uploaded them. This public exposure could then be used to pressure or blackmail the individual for access to the organisation or to elicit funds.
Threat actor-related files can also be found on these services, including stealer logs, blackmail formats, fraud bibles, attack tutorials, and more. This portrays the widespread use of these platforms by both legitimate and illicit entities.
Public exposure from cybersecurity-related operations
Public exposure of sensitive information is not limited to file or document sharing services. Personal information has also been identified on cybersecurity-related platforms such as sandboxing services. For example, users have analysed an EML file from their own inbox or attempted to analyse a referral link which includes their email address. This further highlights the risk of public exposure using services containing sharing capabilities. It demonstrates that employees who may be aware of data handling best practices, such as cybersecurity professionals, can still be subject to unintentional exposure.
Malware analysis sandboxing allows users to download malicious files and analyse the contents in a safe environment with a significantly reduced risk. There is a range of online services which offer sandboxing; however, it appears that these sites are occasionally used to access potentially sensitive content in publicly available scans. This causes unintentional public exposure of data.
In one example, shown in Figure 2, a user attempted to analyse potentially malicious files hosted on a Google Drive folder. However, the files included CVs likely belonging to prospective or current employees of the organisation. This potentially exposed their personal information as these files were accessed during the analysis. Additionally, a possible internal PowerPoint presentation linked to the organisation appeared in the files.
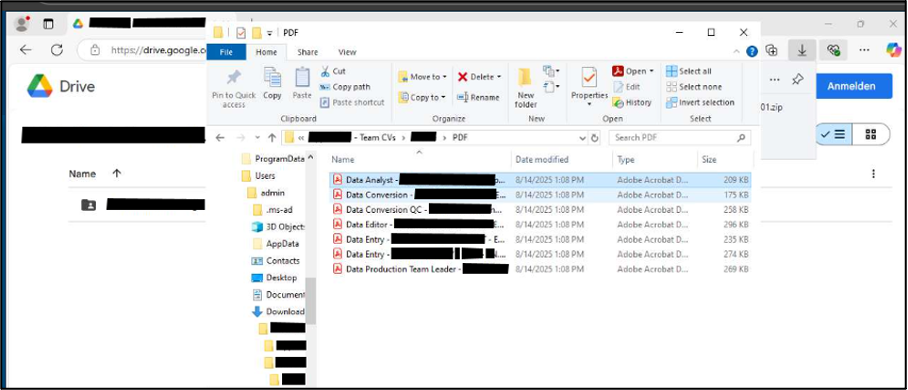
Figure 2 – Example exposure on malware sandboxing.
Another common type of online service is a website focused sandbox. These services are often used to determine whether certain websites are malicious, including phishing links, suspicious domain registrations, user-reported fake domains, and open directories.
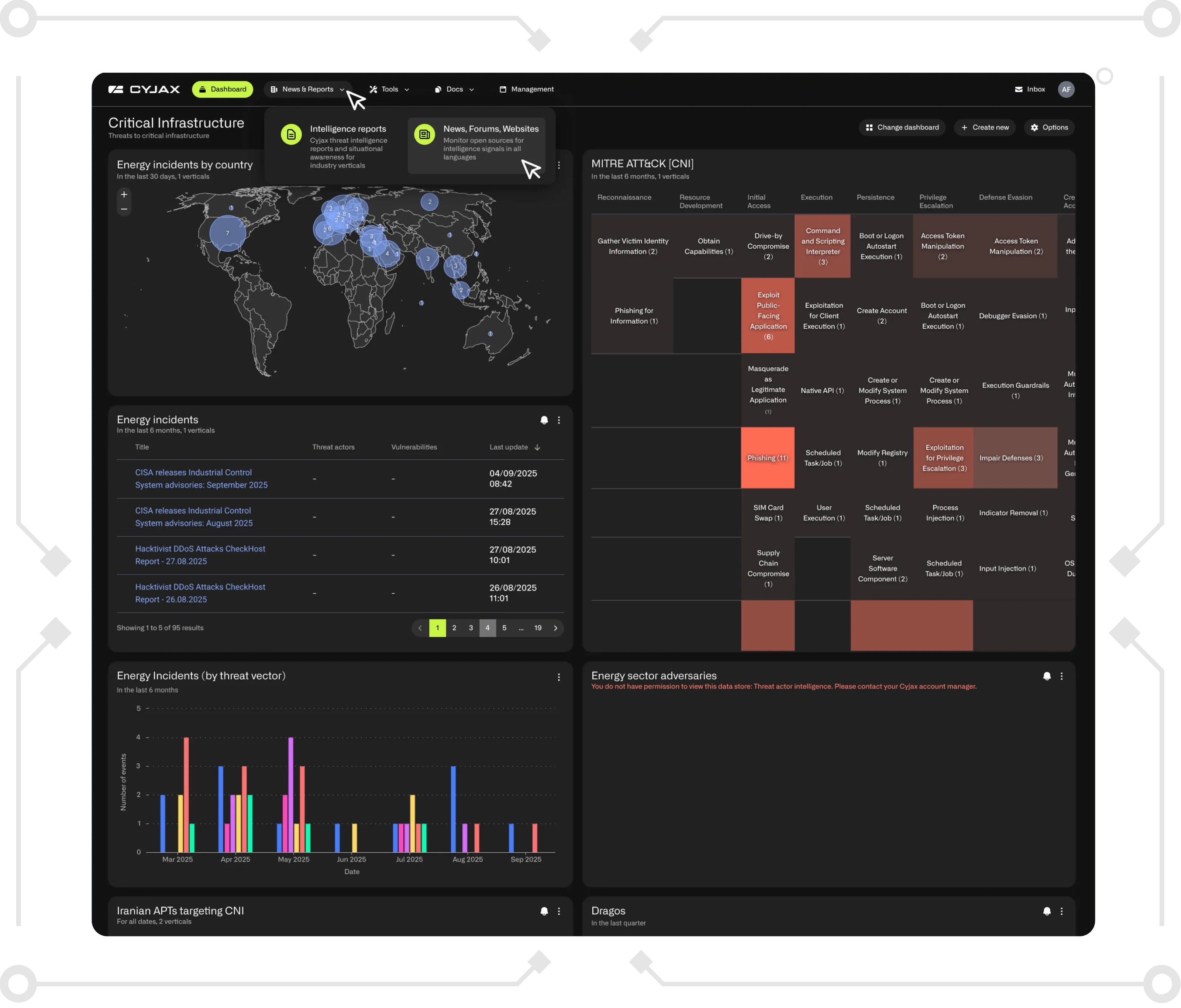
Tracking or advertisement referral links can often contain information regarding the originating source, such as from an email or logged-in service. In some cases, these can include additional personal information such as geolocational data. Commonly observed instances are often from tracking or phishing links and include email addresses, such as the example in Figure 3.

Figure 3 – Example exposure on website sandbox.
This tracking link appears to include an email address in the parameters of the URL, potentially indicating that it was accessed via an email sent to the user. Subsequently, their personal information was exposed when the scan was published.
Conclusions - The importance of document handling
Unintentional public exposure can present a significant threat to organisations. The wide range of exposure across document sharing sites highlights the importance of data control, handling, and compliance. It provides an insight into the potential public exposure of both individuals and organisations.
However, it is important to note that whilst many sensitive documents have been exposed on these services, the platforms are not at fault. From Cyjax’s analysis, it appears likely that many users are unaware of the public nature of the uploaded documents. Consequently, this leads to the accidental exposure of such documents, highlighting the importance of employee training for data handling and security awareness for public exposure. This is to ensure that the importance of document handling is understood throughout an organisation. It is a necessity within organisations but can also help propagate security awareness into personal lives, helping to protect both individuals and businesses from this type of exposure.
CYJAX is an industry-leading threat intelligence solution, helping to protect a wide range of organisations across the globe. If you are interested in learning more about this type of exposure and how it may be affecting your business, please contact the CYJAX team.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.
-3.png)
-2.png)
.png)