Why AI-Only Threat Intelligence Is a Risk Your Organisation Cannot Afford
SaaS-only platforms are betting everything on automation. But when the threat landscape demands judgement, data volume alone is not the answer.

For years, a certain category of threat intelligence vendor has sold the same idea: feed your data into our platform, let the AI process it, and your security team will have everything they need. It is a compelling proposition, particularly for organisations under pressure to demonstrate coverage without expanding headcount. In 2026, though, the gap between what these platforms promise and what they actually deliver is becoming harder to ignore.
The threat landscape has not stood still. State-linked groups like OilRig, Cozy Bear, and Lazarus are continuously adapting their tactics to evade pattern-based detection, and ransomware operations have evolved into modular, highly scalable criminal enterprises. Social engineering campaigns are now being built with AI assistance, making them far more convincing and harder to flag through automated means alone. Against that backdrop, a platform that relies primarily on machine processing to make sense of the threat picture is not a solution; it is a liability dressed up as convenience.
More data, less clarity
Volume has become the default metric for SaaS-only intelligence providers: hundreds of billions of data points ingested daily, thousands of indicators processed in real time, dashboards full of activity. What this model consistently fails to deliver is the thing security teams actually need, clarity on what matters, why it matters, and what to do about it before damage occurs.
83%of SOC teams report struggling with alert volume, a direct consequence of intelligence platforms that prioritise data throughput over contextual relevance.
AI is genuinely capable at certain tasks; processing signals at scale, identifying statistical anomalies, surfacing patterns across large datasets. But it lacks the judgement to interpret ambiguous behaviour, apply geopolitical context, or assess whether a given piece of intelligence is relevant to your specific sector and environment. That distinction requires a skilled analyst, and in the AI-only model, that analyst is not in the room.
AI is accelerating threats, not replacing them
It is worth being precise about what AI is actually doing to the threat landscape, because the picture is more nuanced than much of the industry debate suggests. AI is changing the speed and scale of attacks without necessarily changing their underlying nature. Recent threat reporting shows it is being used to make social engineering more convincing, speed up reconnaissance, accelerate malware development, and automate repetitive stages of the attack lifecycle; making existing techniques faster, cheaper, and harder to detect.
At the same time, AI is also creating genuinely new risks around governance, identity, and shadow-agent behaviour that security teams are still working out how to manage. The challenge for defenders, then, is not simply "AI versus AI"; it is understanding which category a threat falls into and responding accordingly. That kind of contextual reasoning does not emerge from automated processing alone.
"AI is not an incremental shift; it is a force that reorients security. It increases the volume of software, accelerates attacker industrialisation, and makes it harder to trust what is real."
— Phil Venables, Things Are Getting Wild: Re-Tool Everything for Speed
If AI is making attacks faster and more adaptive, then a purely reactive automated defence, one that matches patterns against known signals, will always be a step behind. The asymmetry gets worse over time, not better.
What gets missed when there is no human in the loop
The consequences of over-relying on automated intelligence are operational, not theoretical. 42% of security alerts go uninvestigated, not because teams lack tools, but because the tools generate too much noise to prioritise effectively. Novel attack techniques go unrecognised because AI models are trained on historical patterns, not on what threat actors are doing for the first time. And intelligence becomes disconnected from business context, leaving teams with information they cannot translate into a decision. Manual alert triage is estimated to cost $3.3 billion annually in the US alone, a figure that reflects the real price of volume without judgement.
"CYJAX provided the additional context and filtering we needed to rapidly triage and qualify which alerts need actioning. This freed our team up to make adjustments to our security controls, vastly reducing the number of alerts coming in."
— CTO, UK Power Networks
From visibility to action
The questions security leaders are asking in 2026 are not abstract, they are operational. How do we move from visibility to prioritisation? How do we translate intelligence into action when teams are already stretched? This is where the human-in-the-loop model matters most. Threat intelligence is most valuable when it helps teams decide what to act on, and why it matters now, not when it adds to the pile of things to investigate.
In a world where AI can generate more alerts, more content, and more attack surface, the competitive advantage is not more noise. It is better judgement.
.png)
Technology scales security work. People give it meaning.
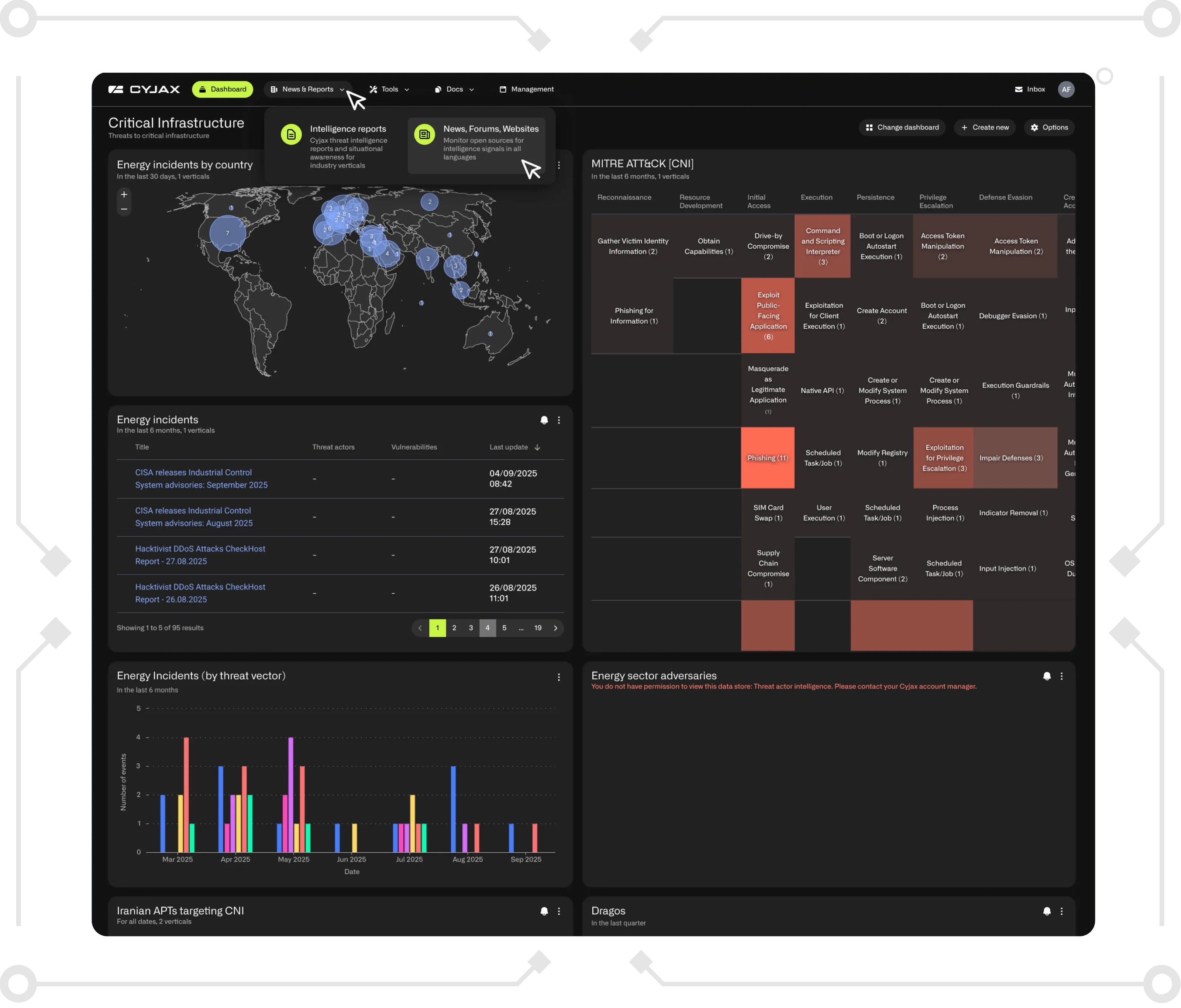
At CYJAX, our platform is built on the belief that technology amplifies what skilled analysts can do, it does not replace them. Our analysts validate signals, apply sector and geographic context, respond to RFIs, and turn fragmented information into intelligence that supports real decisions. That human advantage the capacity to question, interpret, and challenge, is what enables organisations to move from reaction to resilience.
Modern cyber threat intelligence is not just about detecting or countering attacks. It is about understanding the why behind malicious behaviour, anticipating the so what for decision-makers, and translating complex signals into insight that is clear enough to act on. In a threat landscape reshaped by AI, where cyber-attacks have increased 18% year-over-year, the answer to "what do we do next?" will not come from a dashboard. It will come from analysts who understand the context, know your environment, and have the experience to make the call.
See the difference analyst-enriched intelligence makes
CYJAX helps security teams cut through the noise, prioritise genuine threats, and respond with confidence, powered by expert analysts, not just algorithms.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.