Why Alert Fatigue Is Still the Biggest Hidden Cost in Security Teams
Alert fatigue is quietly draining security teams, slowing response times, and increasing business risk. As cyber threats rise and alerts multiply, organisations need smarter prioritisation and actionable intelligence, not more noise.
-3.png)
Cyber Threats Are Rising, But So Is the Noise
Cyber-attacks continue to grow in volume and sophistication. Recent findings show an 18% increase in cyber-attacks year over year, while 82% of malicious file attacks are delivered via email. As threats increase, so does the number of alerts generated by security tools.
For many SOC and threat intelligence teams, the challenge is no longer visibility. It is managing the sheer volume of notifications while identifying which ones actually matter. This pressure is often felt most acutely by lean and mid-sized security teams, where limited headcount means the same analysts are expected to monitor, investigate, and respond around the clock.
Alert fatigue happens when analysts are exposed to a constant stream of alerts, causing genuine threats to be delayed, missed, or ignored. When resources are stretched, even a manageable number of alerts can quickly become overwhelming, increasing the likelihood of missed signals and slower response times. It weakens detection, slows response times, and increases business risk.
The financial impact is significant. Manual alert triage is estimated to cost $3.3 billion annually in the U.S., while 42% of alerts go uninvestigated.
What Causes Alert Fatigue?
1. Too Many False Positives
Not every alert represents real risk. Many security tools generate notifications based on suspicious behaviour without enough context to confirm whether it is malicious.
This means analysts spend valuable time investigating benign activity instead of focusing on genuine threats. When false positives become routine, trust in the alerting system declines.
2. Poor Detection Rule Quality
Outdated or poorly tuned detection rules can create unnecessary noise. Rules that are too broad often trigger excessive alerts, while rules that lack relevance to the organisation’s environment produce low-value results.
Without regular optimisation, alert volumes increase while analyst efficiency drops.
3. Growing Attack Surface, Growing Alert Volumes
Modern organisations operate across cloud environments, remote endpoints, SaaS applications, and third-party suppliers. Every new system adds another stream of telemetry.
More tools and more data often mean more alerts, but not always more clarity.
4. Security Skills Gaps and Understaffing
Many SOCs are expected to defend around the clock with lean teams. When resources are stretched, analysts must process high volumes of alerts under pressure.
This creates fatigue quickly and increases the chance of mistakes.
Why Alert Fatigue Is So Dangerous
Alert fatigue creates serious operational and business risk. When analysts are overwhelmed by constant notifications, genuine threats can remain buried in queues for hours or even days, giving attackers more time to move undetected and increase impact. High-risk alerts may also be dismissed because they resemble the many false positives teams see every day, allowing malicious activity to blend into the noise. Internally, the constant pressure of repetitive triage, long queues, and reactive workloads can damage morale and contribute to burnout, making it harder to retain skilled security professionals. Beyond the SOC, delayed detection can also lead to breaches, regulatory scrutiny, contractual penalties, and insurance complications, particularly if warning alerts were generated but never properly investigated.
Turning Alert Overload Into Actionable Intelligence
Security teams do not need more alerts. They need better prioritisation, stronger context, and clearer decision-making.
That is where intelligence-led security operations make the difference. By combining internal telemetry with external threat intelligence, organisations can cut through noise, identify real risk faster, and improve response confidence.
Alert fatigue may be hidden, but its impact is not. The organisations that address it now will be better positioned to detect threats faster, protect analysts, and reduce long-term security costs.
How CYJAX Helps Reduce Alert Fatigue
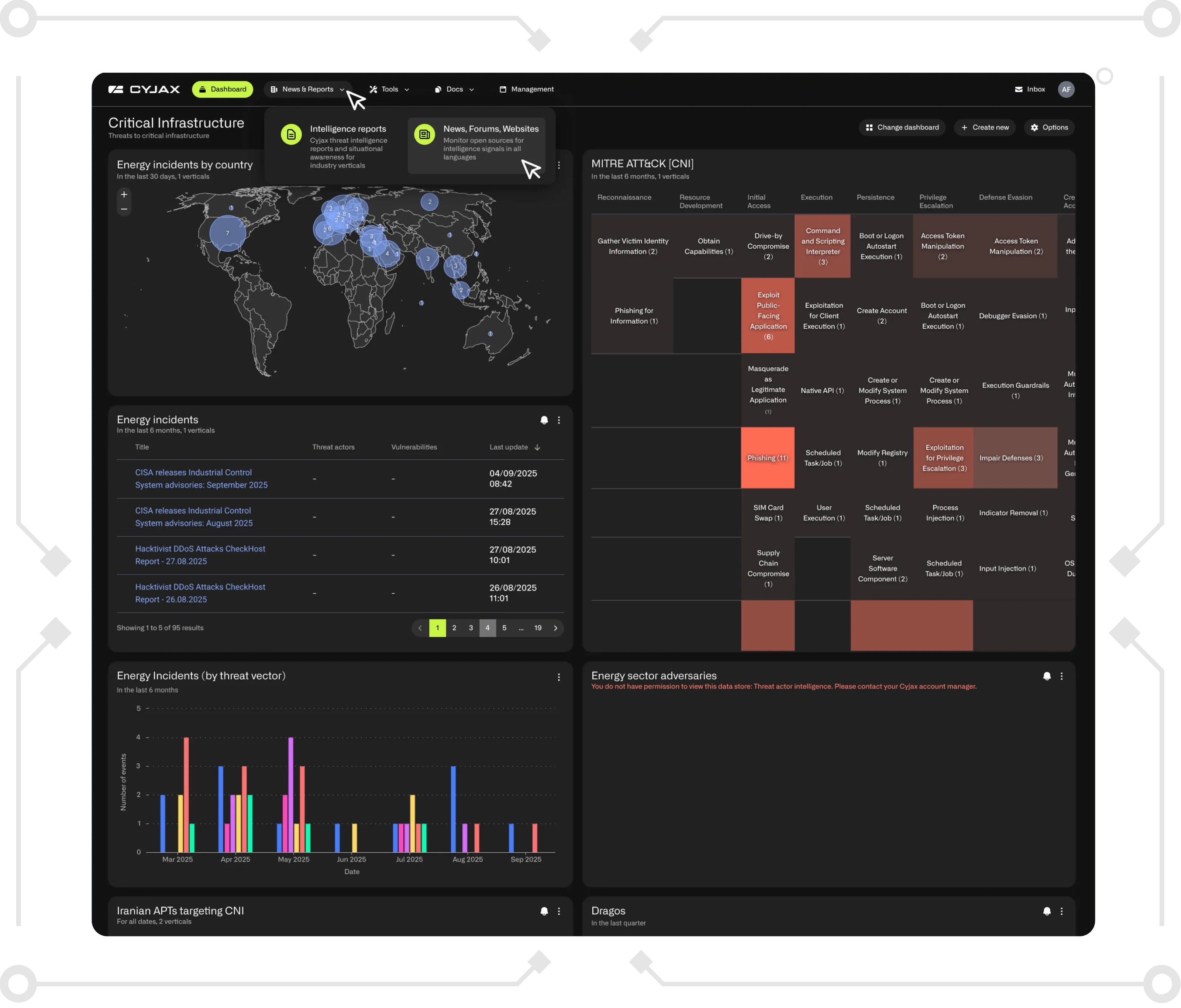
CYJAX helps security teams move from reactive alert handling to proactive threat-led defence. Our intelligence-led platform enriches alerts with context, prioritises genuine threats, and reduces noise so analysts can focus where it matters most.
From dark web monitoring to external attack surface visibility and tailored threat intelligence, CYJAX helps organisations turn overwhelming volumes of data into faster, smarter decisions.
Speak to CYJAX today to see how we can help your team cut through alert noise and strengthen security operations.
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.


-2.png)
.png)