Developments in the conflict between Iran and the US over the last week included the promised retaliatory attacks launched by Tehran in response to the killing by the US of military commander Qassem Soleimani. The strikes on American bases in Iraq did not result in any further loss of life, and the general consensus – at least in the west – was that the immediate likelihood of all-out war between the two countries had decreased significantly.
However, during Iran’s targeted strikes, a Ukrainian airliner crashed as it was taking off from Tehran, resulting in the deaths of 176 people. Iranian officials initially claimed that the plane had come down due to mechanical failure. Yet the evidence readily available online showed this not to be the case.
We talked to an aviation enthusiast and infosec specialist Mike Thompson, who had examined the circumstances surrounding the disaster, and explained the following:
“When the aircraft was reported to have crashed, I fairly quickly took a look at the data available in FlightRadar24. We speculated that it may have been downed by the Iranian military, mainly as it timed roughly with the missile attack on US targets in Iraq. Media reports carried a variety of theories, while Iran insisted engine trouble was the cause, or other mechanical failure. Looking at the data and an understanding of how commercial airliner transponders work, this didn’t seem possible.
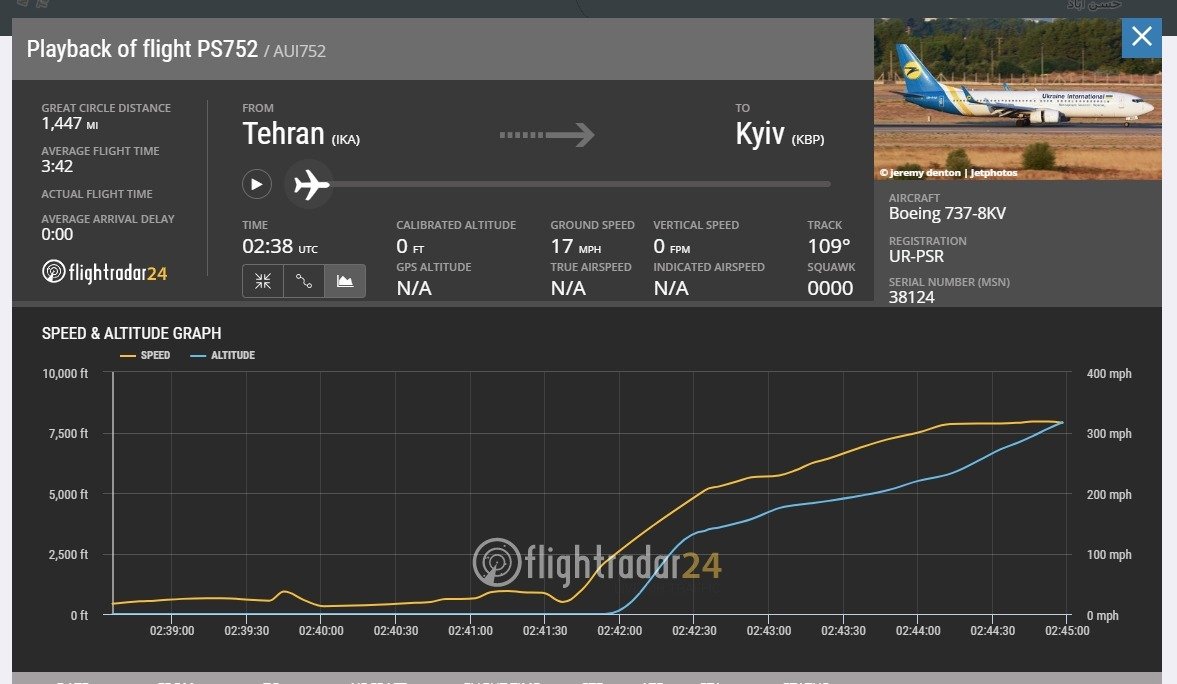
“The chart shows a steady climb rate and speed increase typical of a normal take off. This is fine, except when the aircraft reaches roughly 7500ft and then the data just disappears. Then take a look at this:

“Almost textbook. The airplane taxis fine, hits take off speed and follows a fairly steady heading. Now, more recently, we have been told that the aircraft was trying to return to Tehran airport. The data contradicts this clearly. In my opinion, the ADSB transponder stopped transmitting data as the aircraft was hit by a projectile, causing catastrophic failure both of the integrity of the aircraft and the ability of both it and the crew to report a status.
“The aircraft impacted the surface to the right of its last known location in data, which chimes with it simply losing all control and making a random bank before crashing down.
“We have also seen video released that seems to show a projectile impacting the aircraft. This leads me to conclude that there is no doubt that the flight was downed by the Iranian military. Based on the transponder failing suddenly and no distress calls being made by the crew (despite reports to the contrary), I’d suggest the missile hit the front section of the fuselage, probably near or at the cockpit. Was it deliberate? I doubt it, as it was carrying many Iranian nationals, as well as foreign nationals of Iranian descent. Was it incompetence? Highly likely.” The data is still up on FR24. although they’ve removed the link to it in the flight history. Here’s the URL.”
With this incontrovertible evidence, it was only a matter of time before the Iranians admitted to having shot down the plane in error: 82 Iranians were among the 176 people killed.
Iranian president Hassan Rouhani said: “The Islamic Republic of Iran deeply regrets this disastrous mistake. My thoughts and prayers go to all the mourning families.”
The announcement of culpability led to thousands of people taking to the streets in Tehran and other cities, with footage of angry protests being widely shared on social media.
Demonstrators were reported to be calling for the resignation of senior officials in the ruling regime and shouting anti-government slogans. “They are lying that our enemy is America, our enemy is right here,” a group of protesters chanted, according to video clips posted on Twitter.
What is interesting to note here is that the renewed sense of solidarity and nationalism initiated by the assassination of General Suleiman appears to have been badly impaired. At a time when US sanctions have inflicted severe damage on the Iranian economy, resulting in genuine hardship for many ordinary citizens, the admission of responsibility for shooting down the airliner has led to the regime facing much greater opposition, while support is being voiced for the enemy.
However, for now at least, another escalation in military conflict between the US and Iran appears to have been averted.
When it comes to the prospect of further retaliation taking the form of cyber-attacks launched by either side or indeed their allies, the situation is less clear.
Following our two most recent blogs on cyber-warfare between the US and Iran, we asked our CISO, Ian Thornton-Trump, for his thoughts on the next most likely moves.
Ian noted that the greater the success Iran enjoys in cyber-attacks launched as part of any operation, the more likely the situation will escalate to kinetic and Iranian losses.
He continued: “There is no scenario where Iran wins. The US and its partners have access to the transatlantic cables and ‘relationships’ with most of the global providers, which in the event of a national or international cyber-attack could remove Iran from the Internet. The Americans built the Internet and they can take it away.
“Some research analysts suggest that both China (the American drone napping) and (Russia) Triton malware incident indicate Iran’s engagement with those two nations to either train or conduct operations on their behalf. Shamoon attacks on Saudi Aramco are both historical and relevant to improved capabilities.
“However, the real questions in my mind are: 1) How much compromised infrastructure does Iran already own, and have they made any moves to buy access on the Darknet markets to attractive targets? 2) Do they have zero-day(s) stockpiled to unleash or have they made any moves to buy them? A significant cyber-attack that rises above the threshold of annoying is going to need these two components. We know that some Iranian proxy (companies) were responsible for SamSam ransomware campaigns in the past, but US CERT burned all of that and made the IOCs public along with all the hashes.
“I think any significant cyber-attack by Iran will take weeks if not months to prepare and execute: this is not a situation to be cyber-trigger happy.
“Lastly, why bother? It looks as if public opinion has delivered (at the cost the deaths of Soleimani and other officials) a request from Iraq to the US to pack up and leave. This is pretty much exactly what they wanted to exert – a free rein in Iraq – and move it to their sphere of influence. Why fire a cyber-shot when, if you are smart and playing the long game, you have got your most deadly enemy pushed out of the sandbox?
“A bold cyber-attack may occur, but right now with inflamed sensitivities and Americans being run out, why bother? Terrorists and proxies are a short-term solution to ‘revenge’ and an attack on CNI can be attributed to a wayward squirrel or human mistake. As it turns out, CNI breaks all the time and to rise above the general unreliability attribution, this type of attack would take a lot of effort, preparation and patience.
“An impactful cyber-attack on Saudi Arabia or the UAE seems more likely than confronting America or Israel head on. Right now, with rhetoric flying and everyone being hypersensitive, it seems like the wrong political move. Engaging Russian or Chinese cyber mercenaries to do the dirty cyber-work to eliminate any escalation from the great cyber Satan seems like the smart play.
“So, from a ‘sophisticated’ cyber-attack perspective, I’m wondering if this level of competence is indicative of a huge amount of fear, uncertainty and doubt regarding Iranian cyber expertise or any other military capabilities.”
Here at Cyjax we will continue to monitor the situation in the region, both by keeping an eye on current events and on the possibility of cyber-attacks being launched by either side or, indeed, their allies.
In the meantime, we continue to advise companies operating in the region, particularly those involved in the energy sector, to ensure all software is fully up-to-date, and vigilance in detecting cyber-attacks is maintained.
If you would like to see our coverage of the latest events or background on Iranian cyber-attacks, please see our most recent blogs here and here.
