The Cyber Threat Intelligence Analyst – Speaking Your Language
One issue that is raised frequently is the way in which security or IT teams struggle to speak the “business language” to members of the senior leadership that take the final decisions on spending and investment.
This problem could have its roots in IT - and later security - teams historically having their management lines within the accounting department - they were ultimately accountable to the Chief Financial Officer. Regardless, there was significant potential for an apparently adversarial relationship between those in IT and the decision-makers at the top of the business. Most often we have seen this attributed to poor communication skills, from responses deemed “too technical” to a misalignment with the overall aims of the organisation.
While the majority of departments in any organisation do not live in a binary world of ones and zeros, accounting and IT generally do. It’s on or off, controlled or not. The world inhabited by sales, marketing, customer service and support, human resources and others is one of nuance, emotion and flexibility - it's greyscale, not black and white. Therefore, we are not confident that this is simply a miscommunication problem – this is where an investigation should begin, but it’s not where it ends.
One example is monthly vulnerability management. Is taking key systems down for patching generally a minimal impact event? Probably, unless that activity is executed over the last weekend of each month or quarter when busy salespeople may be working overtime to input customer orders and close key deals to drive revenue. This is just one of a number of situations that are highly likely to cause tension.
Take the situation when organisational execution runs into an IT or security team’s routine of “always patch on the last weekend of every month”. Sales may be upset with IT and/or security. Whereas IT and/or security is of the belief they are doing a great job, they are meeting the vulnerability management SLA. Tension. Anger. Distrust. All disastrous to relationships in private but in a company context, where long-simmering issues fester, this can endanger the organisation's chances of success.
Cybersecurity aligned to business goals
What if there was a group of folks whose mission was to justify the IT or security team’s actions and who were able to base these needs upon the organisation’s appetite for risk? What if it was this group or individual’s job to drive and communicate the proposed activity in concise business-friendly language to those departments that are not aware of the specific IT or security matters? There is. It’s called a Cyber Threat Intelligence (CTI) analyst.
Simply put, a CTI analyst is able to bridge communication gaps by being aware of unique IT, security and business requirements. It’s our belief that proper communication of “facts” that impact the business’ risk tolerance will move an organisation to adopt a more business-friendly and “agile” relationship between all departments. Those who treat IT or security at best disrespectfully and who, at worst, are filled with contempt, will be able to feel a sense of ‘being heard’ as a result, decreasing the likelihood of friction and tension taking the business off track.
To put it another way. You may need an analyst that lives in a world of possible risks whose job is to explain the “what” and the “so, what” to answer all the other departments' and executives' exasperated question of “why?”
Make no mistake: a CTI analyst will be tasked with aligning the challenges in communication language, figuring out the business risks, and ultimately determining what actions are needed to mitigate those risks. All with budget, priorities, and even individual department needs. The keys to this business, IT and security relationship are communication and awareness above all else. They will balance the knowledge of both sides of the business – what are the “crown jewels,” and what are the controls used to protect them?
Intelligence-based growth
Part of the CTI analyst role may be hearing and balancing the needs of internal stakeholders, but an even more valuable part is keeping their ear to the ground and being aware of the industry-wide trends and risks. This is where the ‘threat intelligence’ part of the job comes in: that is, recognising the ever-changing threat landscape and seeing how this can affect your organisation as a whole, as well as on an individual departmental level.
Good CTI analysts are made, not born. In most cases, intelligence analysts are trained by government agencies, law enforcement or the military. But, someone passionate about communicating and justifying disruptive business action based on a creditable threat to the organisation will go a long way in reducing the friction between IT/security and the other parts of the businesses. They will have the training of the ‘real world’ view, technical knowledge and industry best practices, alongside the business focus of your distinct sector. All of this information will then be used together to create a holistic and robust strategy.
Ultimately, this role is not a simple “zeros and ones, patched and not patched” mindset. It’s not even red team, blue team. The CTI analyst role reaches beyond the traditional view of an analyst because they’re uniquely versed in both the technical and human sides of the business, and are able to see trends that might otherwise go unnoticed.
This piece first appeared on Tripwire as a guest authored article and has been modified. The original can be found here.
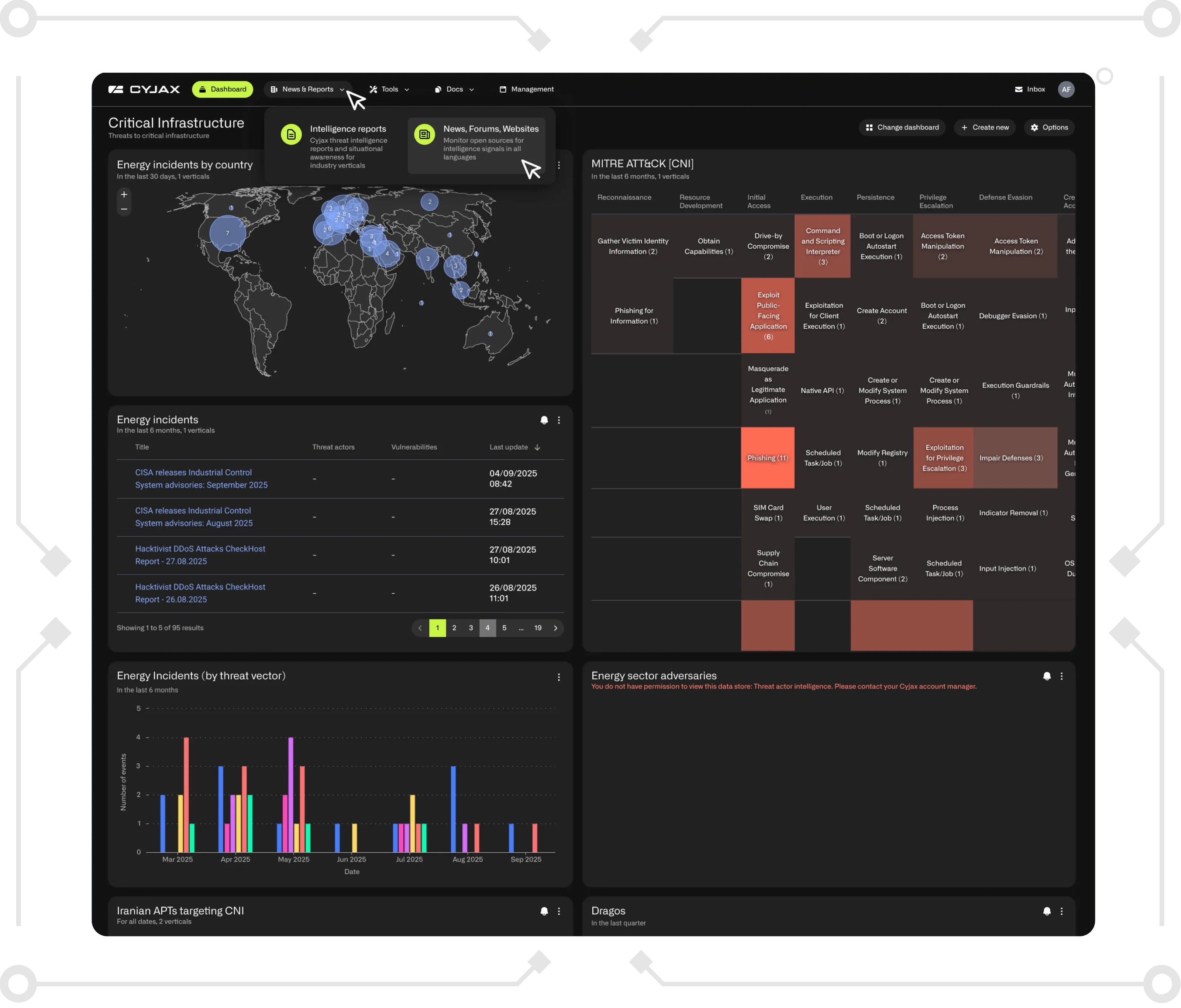
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.