Ransomware Review - November 2021

The Snatch ransomware operators, a group that began operating in 2019 and disappeared in 2020, has resurfaced after almost a year of silence. The group has created a new leaks blog and has already added 10 new victims. They are also one of the multiple groups about which Native American tribes have been warned.An FBI advisory alerted Native American tribes to ongoing ransomware campaigns since as early as 2016 against businesses associated with the tribes, such as casinos, reservations, schools, and emergency services. The groups named by the FBI were REvil, Ryuk, Snatch, Cuba, Conti, and BitPaymer.On 19 November, researchers at ProDraft published a report detailing an operation in which they exploited a vulnerability in the recovery servers of the Conti ransomware group. As a result, they managed to capture the IP addresses of the group's hidden services, as well as gaining access to a management portal for affiliates and the group's victims.The group responded to this attack on its leaks site on 20 November, claiming that some of the statistics from ProDraft’s report were incorrect. Specifically, ProDraft reported that the Conti group had made $25.5 million between July and November. However, in its statement, the group boasted that the total it had made was closer to $300 million, most likely due to other types of cryptocurrencies being used as payments than Bitcoin. Since then, the threat actors appear to be back in full operation unlike its past competitor REvil and have made claims that they are upgrading their malware capabilities.Community Medical Centers (CMC) reported a cyberattack on 2 November that had apparently shut down the non-profit's systems since at least 10 October. The attack was never confirmed as ransomware, however, with the long downtime and destructive nature of the attack it is highly likely that ransomware was responsible. Despite the large leak of 656,047 patients' data, no group has claimed this attack.1 November – Saudi Arabian charity, Alsanie, targeted by Syria-supporting hackers.2 November – HelloKitty ransomware now deploying DDoS as an extortion tactic.2 November – Newfoundland and Labrador healthcare system disclose ransomware attack.2 November – Toronto Transit Commission attacked by ransomware2 November – Las Vegas Cancer Centre victim to ransomware attack2 November – Community Medical Centre disclose ransomware attack, notify 656,047 patients.3 November – National Bank of Pakistan disclose cyberattack.5 November – FBI warns native American tribes of active ransomware campaigns against associated businesses.5 November – MirCop ransomware distributed by phishing campaign5 November – ARM China hit by Conti ransomware.6 November - Danaos Management Consultants targeted in ransomware operation resulting in Supply Chain attack on its customers.8 November – XacBank hit by Hive Ransomware.8 November – MediaMarkt hit by Hive Ransomware.9 November – New Cl0p ransomware campaign observed, attackers exploit SolarWinds.9 November – MedaTixx attacked by ransomware.11 November – Stor-A-File attacked, company appears on Cl0p leaks site.11 November – Premier Property Lawyers hit in disruptive cyberattack.12 November – Magniber ransomware observed using Internet Explorer vulnerabilities for initial access.15 November – Japanese Handa hospital hit in LockBit 2.0 attack.15 November - Rideau Valley Health Center disclose disruptive cyberattack affecting systems from 22 October16 November – Frontier Software discloses ransomware attack18 November – Memento Ransomware observed using ZIP files as a replacement for ransomware.19 November – Vestas Winds Systems victim to disruptive cyberattack.22 November – SugarLocker ransomware group advertises on hacking forum22 November – Charlie Hebdo appears on Everest leaks site.25 November – Supernus Pharmaceuticals appears on Hive leaks site.26 November – Swire Pacific Offshore attacked by Cl0p ransomware.28 November – Snatch leaks site reappears.
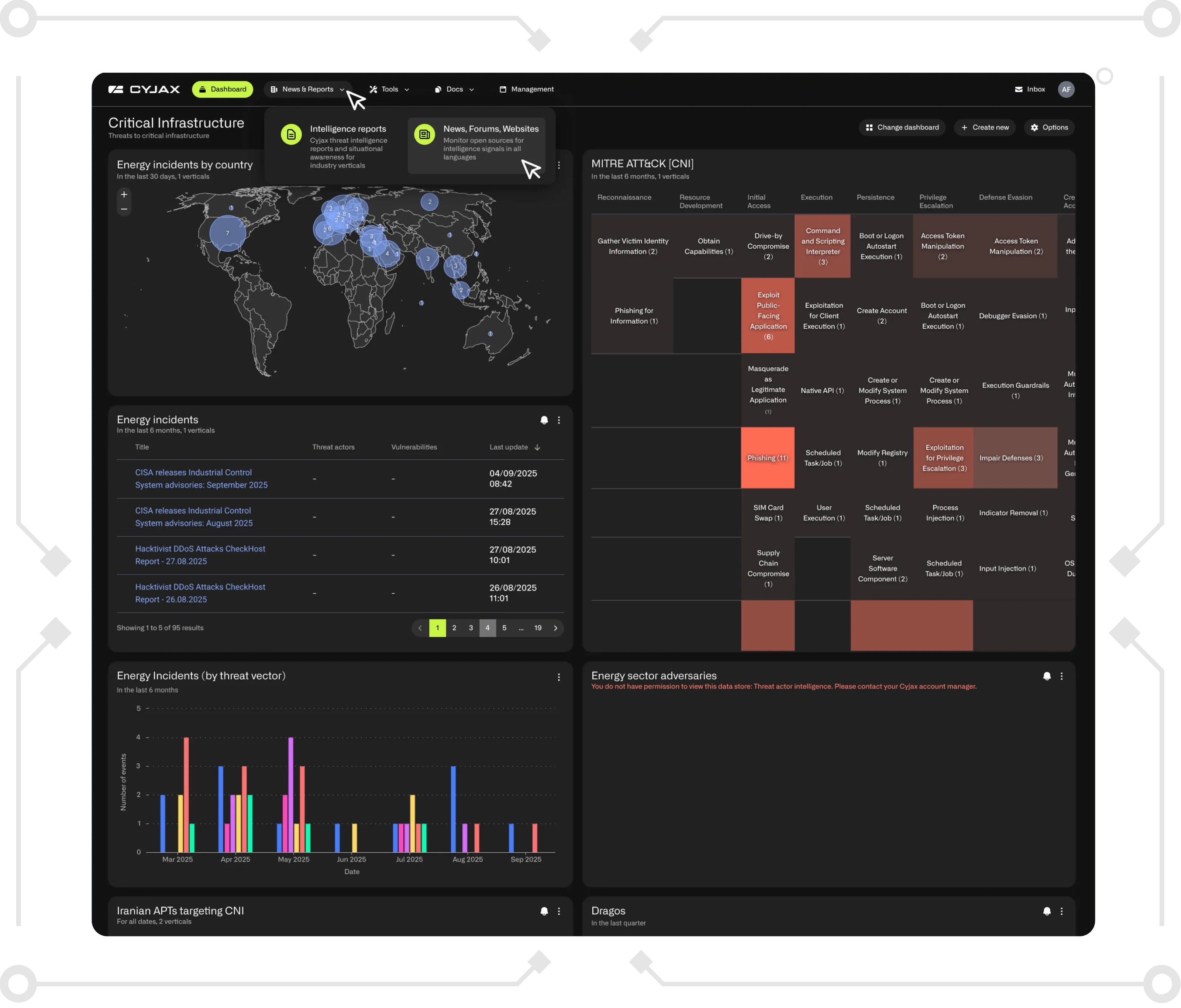
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.