R&D Security Report
Research and Development (R&D) is a vital part of business for many companies and a significant proportion of the GDP of leading global economies. Advanced R&D provides an attractive target for a wide range of attackers seeking to steal the “crown jewels” of intellectual property.R&D activities often involve trying out new technologies. Supply chain security is an important consideration. Open-source software is a highly attractive target for attackers, as anyone can make alterations to the codebase. Many prominent open-source projects rely on dozens of other dependencies, some of which have their own. This complex web of different projects is an ideal environment for attackers to hide in. Advanced attackers can successfully insert vulnerabilities into even the most monitored open-source software. In 2021, researchers from the University of Minnesota published a paper showing how they successfully introduced use-after-free vulnerabilities into the Linux Kernel. Open-source software is often distributed through online repositories such as pypi and NPM. Typosquatted malicious packages (for example, “request” instead of “requests”) uploaded by threat actors are easy to accidentally install through command-line tools.Although espionage was initially seen primarily as a concern only for defence-adjacent industries, the threat landscape has changed. Nation-state economic espionage, especially from the Chinese government, has become far more widespread and indiscriminate. Companies across all verticals are valid targets as the Chinese government seeks to gain a widespread economic advantage over competing countries. In the words of FBI director Christopher Wray, the Chinese Communist party has targeted “companies everywhere from big cities to small towns—from Fortune 100s to start-ups”.The rise of non-governmental APTs also provides a new and unique threat: for example, the Lapsus$ group’s widespread data theft and leakage for nothing more than their own enjoyment. The introduction of double and triple-extortion ransomware tactics has made these attacks significantly harder to mitigate. Even if organisations have backups and restore encrypted data quickly, blackmail from data theft poses a serious reputational and financial risk. Ransomware-as-a-service groups such as ALPHV/BlackCat provide their tools to anyone willing to carry out an attack, leading to a wide variation in TTPs and making detection harder for security authorities.Click here to download the White Paper.
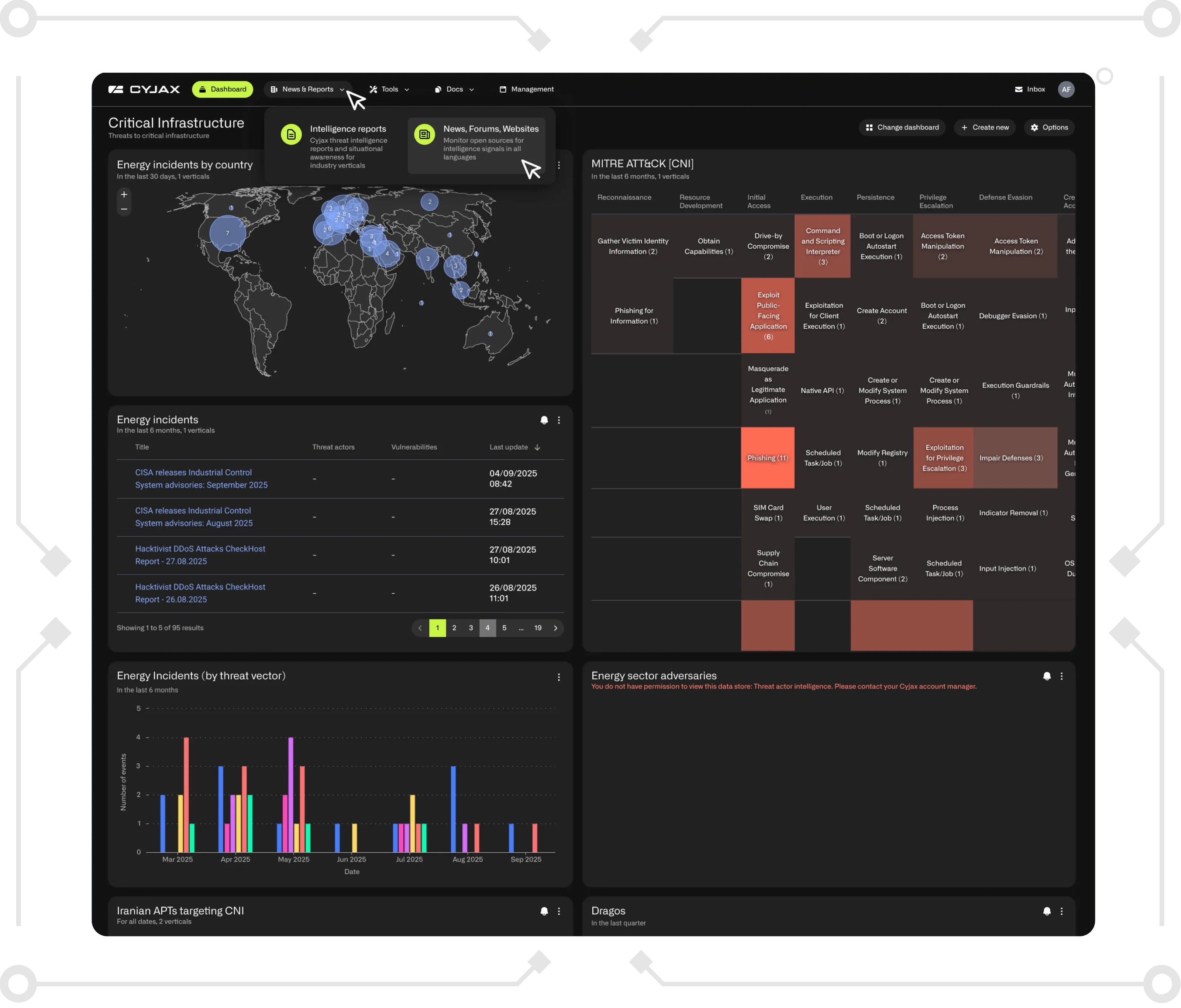
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.