Shodan is an extremely useful tool for checking what devices your network may have listening on the Internet, or for getting an idea of the overall exposure of a type of database or device. We can also use Shodan to find databases that have been routed to the Internet by mistake or databases that do not have any kind of authentication – meaning anyone is able to read, write or delete data over the Internet.
Open Season on ElasticSearch
ElasticSearch is a popular type of database mainly used to store application logs but also used to store any other type of data. Unfortunately, ElasticSearch is often misconfigured by the end-user which results in a database instance routed to the Internet without any authentication at all. This has led to over 20,000 open ElasticSearch instances being discoverable on Shodan alone.

For a while this provided a steady stream of data breaches, some reported in the media and some kept quiet by the respective database owners. One of the more interesting breaches was an Elasticsearch instance containing over 5 billion records, made up from collections of previously exposed usernames, passwords and other data.
This reformulation of previously leaked data continues today. Databases are regularly recycled and resold, often by threat actors who had nothing to do with the initial incursion that resulted in the breach. ‘Leaks’ such as the one described above get covered widely in the press, but are often less impactful than they appear.
Ransomed Instances
After a while, criminals decided to try to make money from these misconfigured instances. Many different types of the same scheme came and went over time, the most recent and the most prolific being the one we have simply dubbed “read_me”:
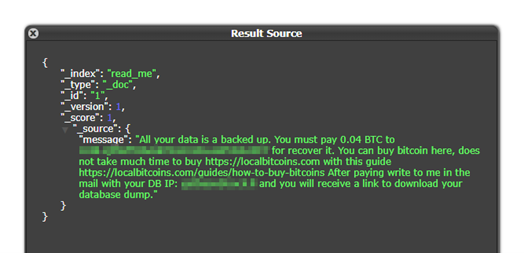
In this case, the threat actors wipe all the indexes (tables) from the ElasticSearch instance and leave a single index containing instructions on how to pay a ransom to get the data back. From what we have observed, however, the threat actors frequently do not back up any of the data and so are simply trying to con the victim into paying, having already erased all the data. Unfortunately, there is no way of knowing this prior to engaging with the cybercriminals and paying a ransom.
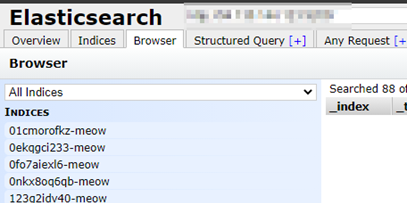
Meow
Meow is a threat actor, with seemingly no financial motivation, who could be described as a kind of Internet janitor (or vigilante). For a significant part of 2020, Meow has been looking for different database instances via Shodan and simply erasing them. The threat actors behind Meow do not leave a note demanding Bitcoin or, indeed, offering any other explanation as to the deletion of the data: they simply rename the tables they have erased to “meow” and move on to the next instance. Little is known about this threat actor, but it can be deduced that they believe they are ‘cleaning up’ the Internet. This behaviour is akin to BrickerBot a piece of malware that would break vulnerable IoT devices, removing them from the Internet.
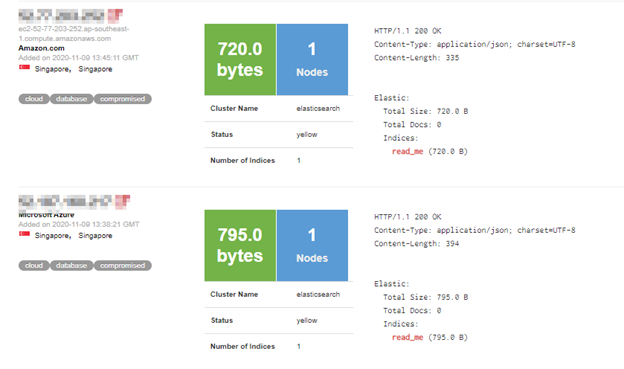
The Wasteland
Searching Shodan for ElasticSearch instances in recent months has turned up page upon page of empty instances. Of the 20,000 pages indexed by Shodan, almost 7,000 have indicators that they have been wiped by Meow and a further 9,000 have been ransomed by ‘read_me’. We are also seeing the same kind of thing happening with MongoDB, CouchDB and Redis instances that have also been left unprotected. What was once a goldmine of data has simply been reduced to a wasteland over a period of a few months. We predict this trend will continue.
In order to protect yourself and your business from these kinds of attacks, it is important to establish exactly what you have listening on the Internet and to implement authentication regardless of whether the service is supposed to be on the Internet or not. A database being exposed for only a few moments could result in the data contained within it being wiped and result in major business disruption.
