Winning with Cyber Threat Intelligence: Taking a More Personal View

In the final article of our trilogy (see the previous articles here and here), we investigate how a cyber threat intelligence (CTI) analyst and programmes associated with this specialism, provide insight about physical and cyber threats to your organisation. The value of these insights is reflected in the 'wins', which come as a result of context building, holistic understanding, and enhanced awareness, that allow you to outmanoeuvre malicious actors.Let’s remember, that a core value of the CTI programme is to do no harm. Ethics plays a significant role in the intelligence field. Any actions taken as a result of gathered intelligence must be carried out under strict review and an assurance that the benefits outweigh the risks. Only in the most serious situation, with potentially grave consequences, should active measures be considered for authorisation. In fact, active measures are the least desirable approach, as they will no doubt reveal the extent and capabilities of your programme.For example, perhaps your intelligence programme receives a tip that a group of criminals are planning to break into one of your facilities. It’s appropriate to issue a reminder to on-site personnel - in order to ensure the alarms are on and the building is secured - and possibly alert the local police force if the tip seems credible. However, it would not be appropriate to deploy untrained employees to ‘defend’ the building from this potential break-in.There are a variety of proactive approaches that mitigate threats, such as appropriate lighting, fencing, visible warning signs and trained security patrols, but requesting untrained employees to take action could put their lives at risk. A recommendation of a reasonable and proportionate response is what the intelligence programme should always offer.
Virtual Kidnapping Scam
This frightening extortion scheme is one in which victims truly believe that their loved ones are at risk of violence or death. As a result, the victim is more likely to pay a ransom. In reality, the loved one is simply prevented from communicating with the victim by a technical measure and is often unaware that their family member or friend is being extorted.Unlike traditional abductions, virtual kidnappers have not actually kidnapped anyone. Instead, through deceptions and threats, the malicious actors coerce victims to quickly pay a ransom before the scheme is discovered; before the loved one reappears.This is a form of social engineering attack, though one that we do not usually discuss. It plays off the same set of emotions that might be triggered by a phishing email – fear, uncertainty, and the ever-present clock counting down until bad things happen.A successful virtual kidnapping can e the result of gaps in operational security (OpSec), such as actively sharing locational data and other information which, when taken together, provides a public picture of the target’s life. Often, this can be carried out through passive monitoring of a target’s social media accounts. A malicious actor can review shared information to determine a target's wealth, associations, friends and social activities to time an attack, and increase the likelihood of payment. If you are interested in learning more about this, we recommend reading the FBI’s article on Virtual Kidnapping.A CTI programme lives in a worst-case scenario view, which includes relevant threat models, understanding of the attack surface, and the constraints on all parties.Implementation of a CTI programme within an educational institution, especially those with wealthy student bodies, would need to anticipate this virtual kidnapping scam along with traditional abductions. They would need to drive proactive actions such as recommendations and/or restrictions of public information, practices, and limiting audience view.Whilst parents are naturally protective of their children, they are also, understandably, proud and wish to share achievements such as pictures of their child's first day of school. These seemingly small mistakes can have big consequences.Applying the threat model:
- Unfortunately, not all audience members viewing a photo of a uniformed child have the best intentions - it’s important to recognise what information in a photograph can reveal.
- When sharing on social media platforms, be aware there’s a chance a profile is viewable to more than the intended audience - often there is no way to know exactly who has viewed an image.
- Sites hosting images might not have a great track record, especially with what the general public knows about the value of their data.
- Not all websites remove the metadata, which reveals where and when a photo was taken.
- Not all photo editors change the file when cropping, it is possible at times to restore to the original version.
- Even when you limit your connections to known contacts, their profiles might not be as restricted, and/or can be used to access information you didn’t realise.
- Limit locational information shared - such as through Instagram photos - until after you have left the location.
- Do not ‘check-in’ to loved ones' homes or share details of your usual routine.
Providing Proactive Recommendations
Limit your audience, make sure you know who you’re sharing a photo or information with, and remove anything that you do not want shared on a global level. When posting photos of children, make the conscious decision whether or not faces should be included – this is a decision both you and your child should be a part of. Remove or blur labelled items, consider if a blank wall is a better option than the back garden.
Countering Business Email Compromise attacks (BEC)
Cybercriminals compromise email systems – often by poorly secured Office 365 or Outlook Web Access (OWA) accounts. Sometimes these criminals use social engineering tactics to gain information about corporate payment or payroll systems. They can deceive company employees into transferring money into a new bank account, using an updated invoice that was legitimate – also commonly referred to as invoice redirection scams. The FBI reports that $3.5 Billion was lost to cyber-crime in 2019: the main source of cybercriminal profit was Business Email Compromise attacks.CTI programmes would identify BEC attacks as a key risk to organisations, especially those that invoice and pay many large accounts. This, therefore, provides an analysis of the processes and procedures for accounts payable/receivable.Requests for a change in banking information from legitimate invoices, or even completely fictitious invoices in the first place, are all different aspects of this sort of financial attack. For individuals, it could be as simple as discounted gift cards, where they cost £10 for £100 card credit.Organisations both large and small have fallen for this attack. Some of the more notable examples include Google paying $23 million and Facebook $100 million to cybercriminals who simply sent them invoices. Another example, that includes misuse of their position as well as fraud, was an insider threat who registered a company and invoiced his employer for hardware that didn’t exist; earning a total of £4.6 million over four years.
Providing Proactive Recommendations
- Verify all requests to update or change banking, payroll or any financial information.
- Make this verification through communication channels that have previously been confirmed as secure – such as a telephone call.
- Confirm the identity of the individual requesting the change using an out-of-band method - a telephone call on a known number.
- Never respond to any urgent requests via email or chat without verifying and confirming the identity of the requestor. If they call you, request to call them back on a known number – remember even caller ID can be faked.
- If any suspicions remain, ask someone else to verify the transaction.
- Set up executives with code words or authorisation codes, prior to an incident, and request this before proceeding with the transaction.
- Implement separation of duties, so no one person can sign off invoices.
- Have a role rotation schedule that limits a person’s capability to abuse their position. This rotation can include mandatory holiday leave.
Spotting an Attack Before it Occurs
There are a number of sources of information on the internet which can be leveraged into an early warning of an impending attack. Being on the lookout for those signs is the primary job of a CTI programme. In order to conduct a typical cyberattack, the malicious actors must complete several steps – some of which can be noticeable, such as active information gathering, or even passive gathering if monitoring specific sources.A typical cyberattack, delivered by a phishing campaign to an organisation, requires infrastructure. In order to send the email, launch an exploit, deploy and control a Trojan and order it to download a ransomware payload, for example, infrastructure must either be owned or rented via software-as-a-service offerings.Prior to interacting within the organisation’s environment, what can organisations look for? Consider the attack that is commonly seen in a phishing email: similar-looking domains. Known as typosquatting, and URL hijacking, these forms of attack rely on typographical errors, small differences that are likely to go unnoticed and confuse users into thinking an email was from a legitimate sender or that a URL links to a legitimate site. RoseSec[.]com is legitimate whereas RoséSec[.]com is not due to the accent over the 'e'. While it is obvious in this article, could you see it on your phone with its smaller typeface?All of these attacks with fake domains, certificate registrations and hosted infrastructure are indicators of a malicious actor potentially getting ready to attack. Even if you remain unaware of this first layer, the early stages of attack can also be detected. Threat actors have to gain system access which involves interacting with your environment, making changes to systems and possibly even disrupting services.By identifying these signs, a good CTI programme can make recommendations like:
- Additional but tailored awareness training to employees with specific roles that may be impacted.
- An awareness campaign, such as advising users to never enter their credentials into a link launched from an email, navigating to sites manually.
- Make use of password managers rather than saving credentials in-browser, and allowing that password manager to support identifying it a URL is known or unknown for an account.
- Alert the network team/email filter to block inbound and outbound communications from specific locations such as an IP address or domain name.
- Report the domain as malicious to the registrar, and investigate any host resolving to that domain and ask for that infrastructure to be taken down.
- Monitoring data breach sources, just like the previously mentioned intelligence feeds. These sources provide insight into sources that could be used to compromise the organisation. such as credential stuffing or reuse.
- Signing up for alerting on resources such as HaveIBeenPwned.com allows organisations to track if a user account has been compromised in a data breach, therefore requiring additional monitoring, password changes, or further restrictions depending on the account’s access.
These are just a few of the many examples we have seen where a CTI programme and good analysis can prevent a major security issue from personal, physical, and professional environments. These CTI programmes have helped thwart serious cyberattacks against the organisation and provided wins that can be used to enhance existing security controls. Often, following a win these CTI programmes share internally, not just to build awareness, but also to highlight the value of seemingly small indicators and encouraging discussions. These wins are also used to monitor for any identification of trends.Knowing that malicious actors are using OSINT, and intelligence within their targets to enhance their chance of success, organisations should be making use of these techniques as well, in order to identify and reduce their chances. Whilst we aren’t saying CTI programmes will remove all risk: we are saying these insights will strengthen an existing security programme and eats, make the organisation more resilient.About the Authors: Ian Thornton-Trump, CD is an ITIL certified IT professional with 25 years of experience in IT security and information technology. Today, as Chief Information Security Officer for Cyjax Ltd., Ian brings to bear his significant experience concerning the threats faced by small and medium-sized businesses, and enterprises. His research and background have made him a sought-after cybersecurity consultant specialising in cyber threat intelligence programs for all sizes of organisation. From 1989 to 1992, Ian served with the Canadian Forces (CF), Military Intelligence Branch; in 2002, he joined the CF Military Police Reserves and retired as a Public Affairs Officer in 2013. After a year with the RCMP as a Criminal Intelligence Analyst, Ian worked as a cybersecurity analyst and consultant for multi-national insurance, banking and regional healthcare. His most memorable role was being a project manager, specialising in cybersecurity for the Canadian Museum of Human Rights. In his spare time, Ian teaches cybersecurity and IT business courses for CompTIA as part of their global faculty and is the lead architect for Cyber Titan, Canada’s program to encourage the next generation of cyber professionals.Zoë Rose is a highly regarded cybersecurity specialist, who helps her clients better identify and manage their vulnerabilities and embed effective cyber-resilience across their organisations. Zoë is a Cisco Champion and certified Splunk Architect, who frequently speaks at international conferences. Recognized in the 50 most influential women in cybersecurity UK for the past two years, and the PrivSec 200, Zoë is regularly approached for media comment, has presented on National News, been featured in Vogue Magazine, and was the spokesperson for Nationwide’s Over Sharing campaign that had a reach of 306 million citizens.
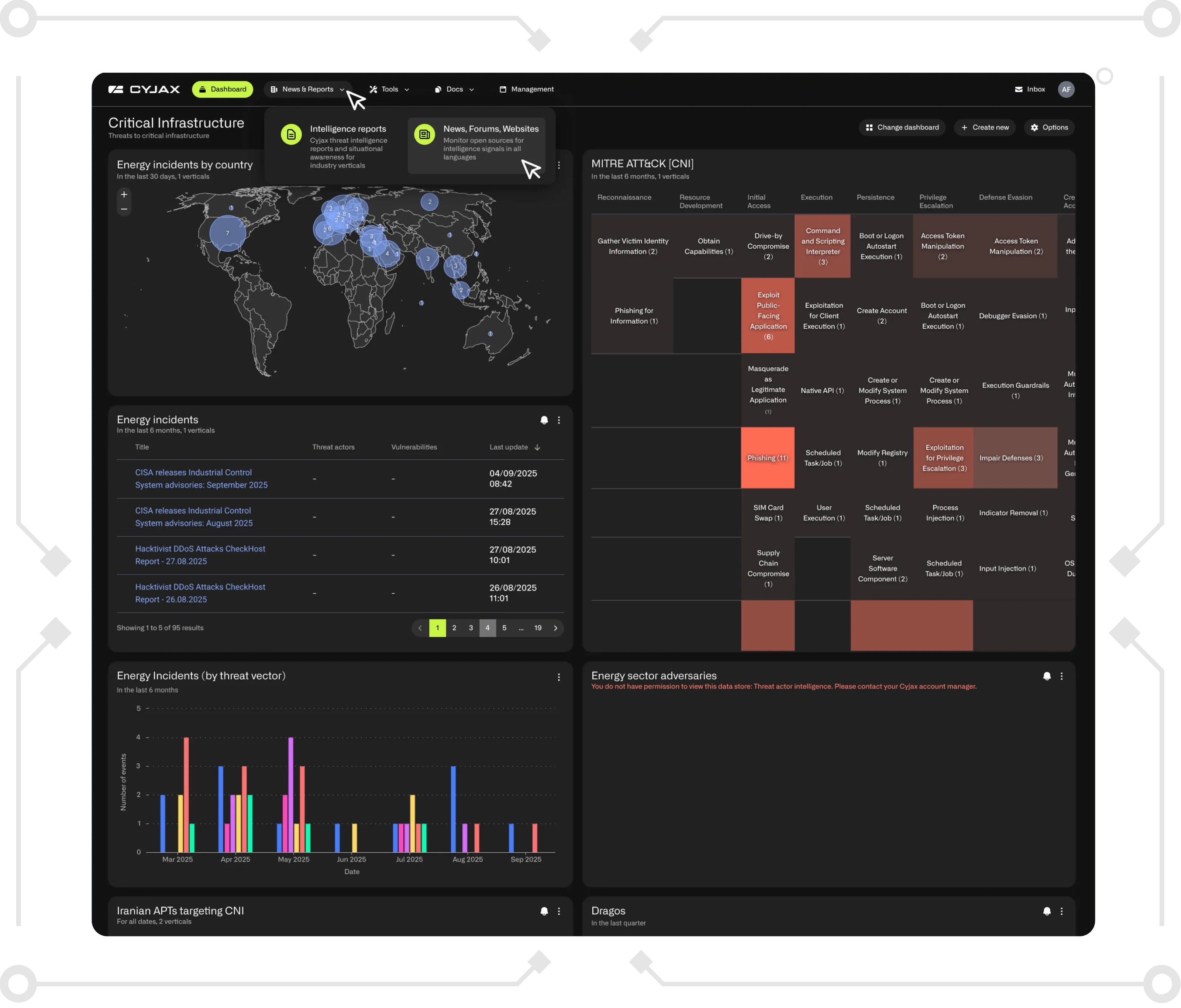
Get Started with CYJAX CTI
Empower Your Team. Strengthen Your Defences.CYJAX gives you the intelligence advantage: clear, validated insights that let your team act fast without being buried in noise.