Over the course of the summer, we observed a marked and significant development in the malspam environment. One malware in particular started to stand out as the payload of choice for threat actors looking to prey on unsuspecting users: the Trickbot banking Trojan.
Detections of Trickbot grew exponentially over June, July and August, with our own spambot picking up hundreds of emails on a daily basis, impersonating well-known financial institutions, as well as the odd telecoms company. This trend could be discerned across the cybersecurity community as a whole, with many attributing the clear uptick in malspam dropping Trickbot to the malware’s relatively new connection to the Necurs botnet, and the greater spamming power that this afforded the malicious actors behind these campaigns.
As well as becoming more prevalent, Trickbot became more sophisticated. New variants were being produced at a prodigious rate: in August alone, some 13 different iterations of the Trickbot family were detected. More than 50 variants are known to be active in the wild at the time of writing. The malware’s target list grew and grew, with the USA being introduced into its list of targeted countries, and it has been established as one of the major threats in the malspam environment for the foreseeable future.
Trickbot first appeared in late 2016. As mentioned above, it is a banking Trojan that originally targeted banks in the UK, across Europe and Australia, as well in as a host of other countries. Trickbot’s entire raison d’être is to steal the financial credentials and information of infected users by injecting malicious code into a web browser process and gathering the details when one of the banking websites that it is programmed to target is visited. It is widely accepted that Trickbot is the immediate successor of the Dyreza (also known as Dyre) malware, and that it is the work of the same developers because, though it has been written from scratch, it contains many similar features to its predecessor. When it was first encountered, it was being distributed via a malvertising campaign driven by the RIG exploit kit (EK).
A large number of financial institutions have been spoofed in these recent malspam emails: they include Lloyds, HSBC, NatWest and RBS from the UK, alongside Santander, Danske Bank, Bankwest, and the Canadian Imperial Bank of Commerce (CIBC). The target list contains banks in countries around the world, and while there has been a recent specific focus on the USA, Trickbot variants over the summer targeted institutions from UK, France, Spain, some Nordic countries, Australia and New Zealand. One particular campaign, dubbed ‘mac1’, which was seen in mid- to late-July targeted various institutions in Norway, Sweden, Iceland, Finland, Italy, Switzerland, Luxembourg, Belgium, Singapore and Denmark, as well as the countries named above.
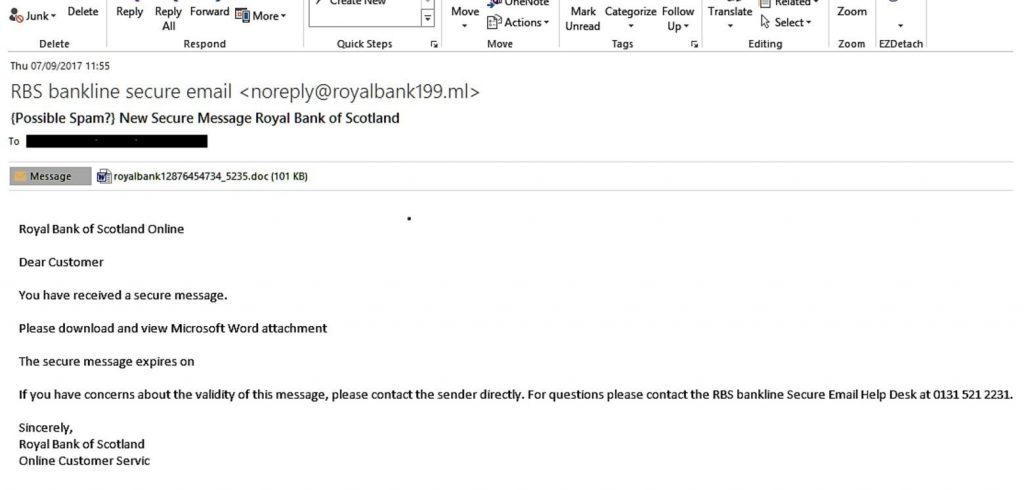
In the latest malspam emails that our spambot picked up, the vast majority would arrive from a spoofed domain purporting to be a well-known financial institution, and containing a malicious Microsoft Word document that, when opened, acts a loader that executes the Trickbot Trojan on the victim’s computer. Occasionally we have seen instances in which emails contain a link to a malicious or compromised domain or, instead of a malicious Word attachment being used as the delivery vector, a .ZIP or .exe file that, when opened, immediately executes the loader.
There are several developments that have been observed in the Trickbot campaigns and the malware itself that have made it an interesting case study, and ensured that the cybersecurity community is keeping a weather eye on this threat. Firstly, the fact that the Trojan is now being distributed by the Necurs botnet. This is a major advance for campaigns pushing Trickbot because of the power of Necurs which first emerged in 2012 and has traditionally been associated with Locky and Jaff ransomware: it is notorious for its massive, malware-laden spam campaigns. The partnership was first observed in the ‘mac1’ campaign mentioned above, and was notable for another reason, the second major development that came about in the life of Trickbot over the summer, the targeting of the USA.
The inclusion of the USA in Trickbot’s target list was important. Until 17 July, when ‘mac1’ was first observed, the Trojan’s webinject configuration had only targeted financial institutions outside the US, but the ‘mac1’ iteration contained an expanded webinject configuration developed to target and infect customers of both international and US-based financial institutions. This trend towards US institutions continued over the summer. One analysis of ‘version 32’ by F5 Labs (the firm reports 51 variants in the wild – see here) found that the target list for that iteration was the largest ever seen for Trickbot, containing 1,366 potential targets. The top targets for ‘version 32’ were CitiBank, Chase, PayPal, Credit Suisse, Nordea, Danske Bank, American Express, Bank of America and Discover. The preponderance of US banks and credit card providers is notable.
The third major development in Trickbot’s summer evolution was the addition of a worm propagation module, ‘worm64DII’, in Trickbot ‘1000029’ (named by Flashpoint) which spreads locally to other computers connected to the originally infected terminal through the Server Message Block (SMB). Vulnerabilities affecting the SMB have been well-documented this year, having been integral to the destructive success of, to name just one, the WannaCry outbreak in May 2017. Relatively reassuringly, however, this module does not appear to randomly scan external IPs for SMB connections, as WannaCry did to such devastating effect.
Clearly, then, Trickbot is a major threat. The developers behind it appear to be industrious, creative and devious. Examples of malspam from almost all the major UK financial institutions have been seen and, to the unsuspecting user, may appear genuine. Typically, they are written well enough to be convincing, particularly for users reading the emails on mobile devices, such as phone or tablets, which only show the sender’s name in the ‘From:’ box, and not the domain from which the email has originated. This is one of the major reasons why these scams and phishing campaigns work so well.
Now, with reports that some iterations of the Trojan contain code for an overlay for a fake Coinbase login page, it appears that cryptocurrency is not safe either. Coinbase is currently one of the biggest cryptocurrency wallets. It is hard to foresee a drop off in the success rate of these malspam emails. As the major security risk is the human factor, the threat actors behind Trickbot, and other campaigns like it, will continue to reap the rewards of curiosity and human frailty.
