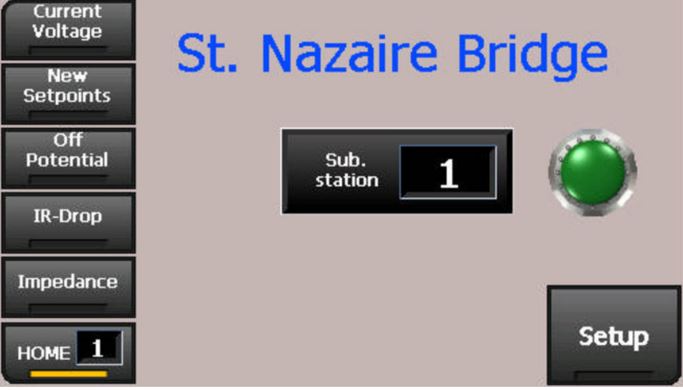
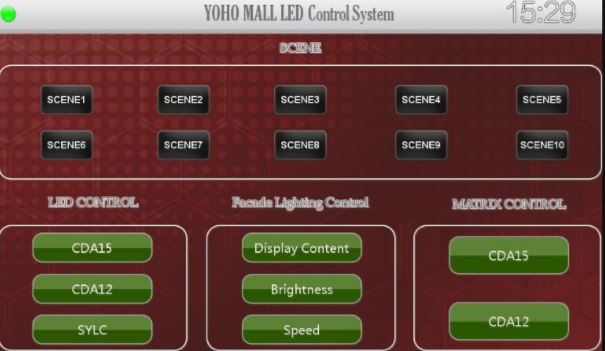
Virtual Network Computing (VNC) allows users to remotely access a range of computer equipment and devices, including desktop machines, smart home systems, electrical substations, mall and gallery lighting control panels, filtration systems, and much more.
Everyone appreciates a bit of convenience and flexibility when it comes to remote access computing, but this should not be at the expense of the potential dangers now on the rise in cyber-physical security. And what we have found in our research is that many systems are vulnerable due to VNC misconfiguration. This sort of carelessness could lead to a very undesirable situation.
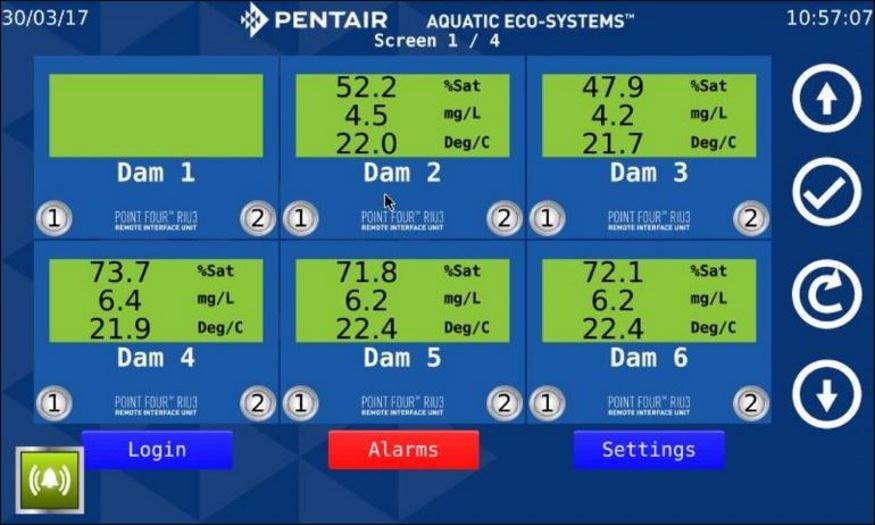
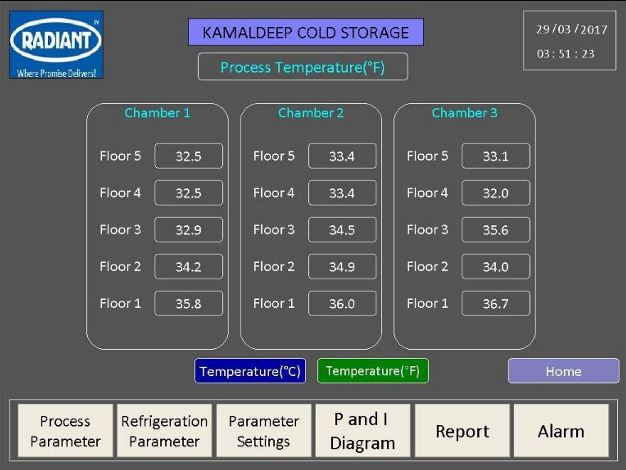
It is now easier than ever to track vulnerable Internet-connected systems using publically available tools such as Shodan. We carried out some extensive research and have discovered a plethora of exposed systems that have been connected to VNC but with authentication disabled. It would be very easy to access any of these systems using special software and control them remotely. While the unhindered ability to control lighting systems may not cause a major problem, open access to water treatment systems including flow and temperature could have catastrophic consequences. Access to cyber-physical systems in the hands of malicious actors could be a disastrous scenario.
So what are some examples of the types of systems we found?
Here is brief a rundown of what we discovered:
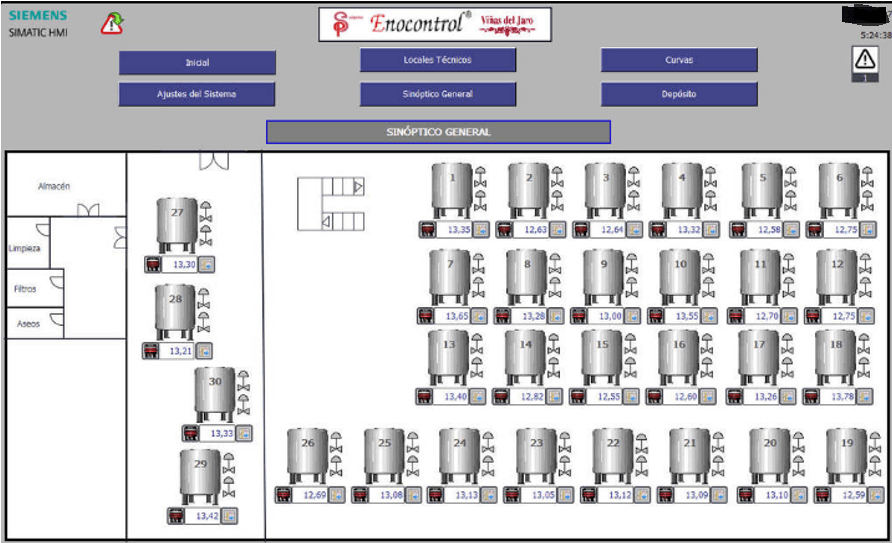
The following system appears to be a Spanish winery and has been labelled as an Industrial Control System (ICS). It has since been taken offline:
Other instances of exposed industrial systems include the following:
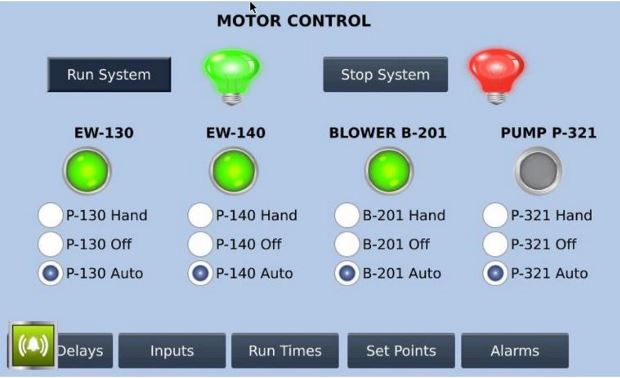
A Steuler industrial corrosion protection system primarily used for power plants was discovered exposed on port 5900 and with authentication disabled. The system can be easily controlled by using a virtual network computing (VNC) viewer.
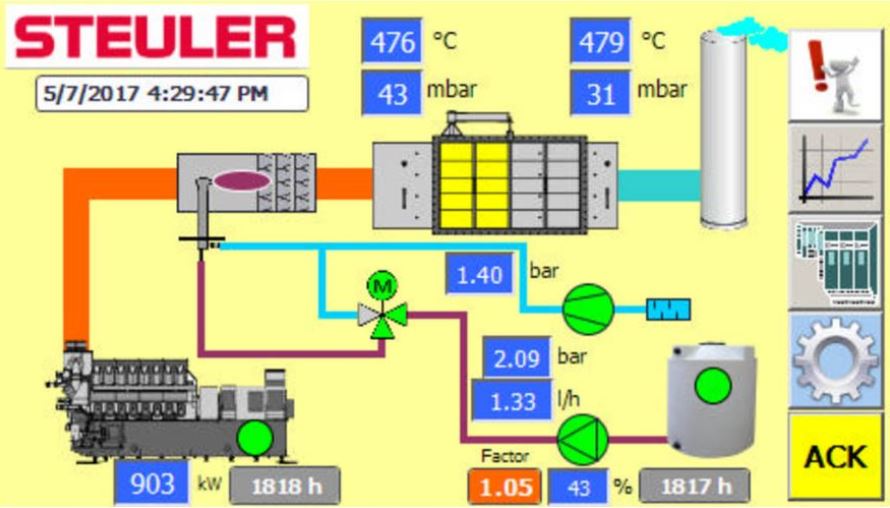
According to Steuler’s website, they "deliver complete corrosion protection systems for bituminous coal, lignite and heavy oil power plants, hydroelectric plants and nuclear power stations".
Although it is difficult to determine the particular system which this is providing corrosive protection for, clearly this could have a detrimental impact on nuclear power stations.s.

VNC can also be established for remote desktop activities such as for accessing files, some of which may be sensitive. An insecure connection has the potential to present a data leak. In the following instance, we see some patient records for a veterinary hospital. Although this mainly comprises a database of animal patients, their owners’ details are attached. With GDPR coming, this is the sort of mistake that could cost you your business.
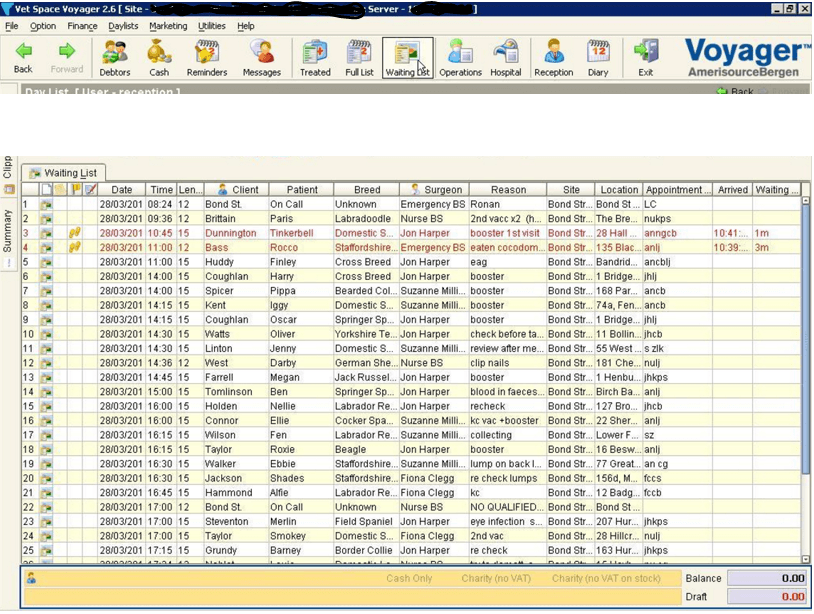
The main cause of these exposures is simply due to VNC misconfiguration: enabling authentication in each of these instances would essentially solve the problem. This is something that is not going away unless we insist on out-of-the-box security for all internet-connected equipment.
With the ever-increasing number of devices connecting to the internet every day, the security industry must make this a priority.
