Vulnerabilities are ubiquitous across nearly everyone’s network infrastructure, and managing them is a monumental task. Staying on top of these flaws is extremely important as they present a viable infection vector for threat actors. Although it is not always an option to patch certain vulnerabilities without a negative knock-on effect to other software, it is important to understand what exploits are publicly available. Threat actors will take advantage of them in order to advance their objectives.
In this report, we outline some of the major threat actors that are actively exploiting vulnerabilities in order to breach systems across a myriad of industry verticals all over the world.
Iranian threat actors have been busy in recent months, with some of them using each other’s code and infrastructure, making attribution to a single actor extremely difficult. What we note is the widespread use of CVE exploits to infiltrate systems and distribute malware.
Just this week, reports surfaced that an Iranian threat actor known as @APT34 or @OilRig has been exploiting the Microsoft Office Memory Corruption Vulnerability (CVE-2017-11882) in order to install a malware payload that ultimately opens a backdoor on infected systems. This is a serious 17-year-old vulnerability that has just been recently patched by Microsoft. Details on this exploit are publicly available and can be found here.
Further, this same threat actor, along with three others, has been exploiting a Microsoft remote code execution (RCE) vulnerability (CVE-2017-0199) to deliver malware payloads. @APT34 targets a range of industry verticals including the finance, government, energy, chemical and telecommunications sectors.
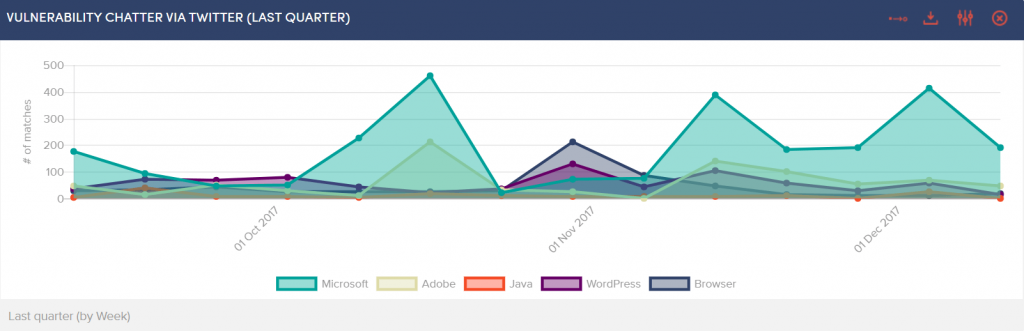
@BlackOasis, another Middle East threat actor, has been exploiting six different CVEs primarily targeting UN officials, opposition bloggers, activists, regional reporters, and others with connections to oil, money laundering and illicit activities located all over the globe. The vulnerabilities have been discovered in Microsoft and Adobe software along with publicly available exploits.
Russian threat actors also tend to use CVE vulnerabilities quite extensively. @APT28, best known for their meddling in US elections, have attempted to exploit at least fifteen different vulnerabilities dating back to 2010. Affected software includes Microsoft, Apache, Adobe, Drupal and Java. It should be noted that these exploits are used in part to deliver a sophisticated arsenal of malware and to further penetrate systems and remain persistent.
In some cases, threat actors leverage vulnerability exploits as well as abusing design features within software that cannot be patched. APT @Carbanak (aka @FIN7) has exploited a plethora of CVE flaws over the past several years. However, it is not always as easy as simply applying a patch; more recently the group has also been abusing the Microsoft Dynamic Data Exchange (DDE) feature which is normally used to transfer data between applications using shared memory. Hacker groups such as @Carbanak are able to leverage this functionality to deliver malware. They have widely targeted financial institutions, professional services organisations and software companies.
Threat actors rely on lackadaisical patching practices – and this is something we have seen again and again. This year, we observed multiple ransomware attacks that included a leaked NSA exploit targeting the now famous SMBv1 vulnerability (MS17-010). The patch was released by Microsoft in March 2017, nearly two months before we saw the first ransomware attack (WannaCry) in May 2017.
It was evident that the flaw had not been widely fixed, and as a result, the ransomware infection was able to spread at a rate we had never seen before. Fast forward to the end of June, and yet another attack (NotPetya) employed the exact same vulnerability: many systems were still unpatched. At this point, you would have thought that companies and organisations would have finally learned the lesson; but yet another attack was experienced in late October (Bad Rabbit) using the same vulnerability once more.
We help our clients track the latest vulnerabilities against their internal asset register, and we also provide details about threat actor tactics, techniques and procedures (TTPs) and indicators of compromise (IOCs) for a more complete picture of emerging threats. Maintaining visibility around who is attacking, how and why, is important from a cyber threat intelligence perspective. As patching systems is an extremely arduous task, in-depth situational awareness is of critical importance, so that one can triage the vulnerabilities that are being targeted first and better protect the network infrastructure.
